About the Execution of ITS-Tools for ShieldRVt-PT-004A
| Execution Summary | |||||
| Max Memory Used (MB) |
Time wait (ms) | CPU Usage (ms) | I/O Wait (ms) | Computed Result | Execution Status |
| 15742.270 | 4146.00 | 9512.00 | 194.10 | FFTFFFFFTFFTFFFF | normal |
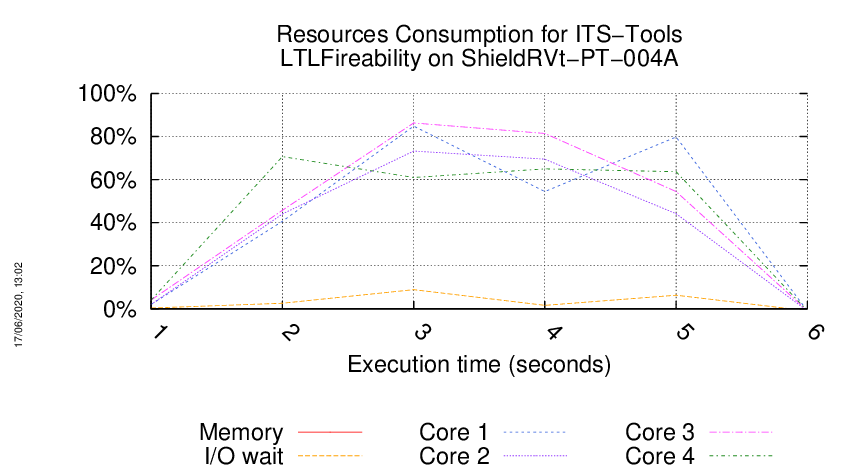
Execution Chart
We display below the execution chart for this examination (boot time has been removed).
Trace from the execution
Formatting '/mnt/tpsp/fkordon/mcc2020-input.r210-tajo-159033476500970.qcow2', fmt=qcow2 size=4294967296 backing_file='/mnt/tpsp/fkordon/mcc2020-input.qcow2' encryption=off cluster_size=65536 lazy_refcounts=off
Waiting for the VM to be ready (probing ssh)
......................
=====================================================================
Generated by BenchKit 2-4028
Executing tool itstools
Input is ShieldRVt-PT-004A, examination is LTLFireability
Time confinement is 3600 seconds
Memory confinement is 16384 MBytes
Number of cores is 4
Run identifier is r210-tajo-159033476500970
=====================================================================
--------------------
preparation of the directory to be used:
/home/mcc/execution
total 176K
-rw-r--r-- 1 mcc users 2.9K May 14 02:36 CTLCardinality.txt
-rw-r--r-- 1 mcc users 16K May 14 02:36 CTLCardinality.xml
-rw-r--r-- 1 mcc users 2.4K May 13 20:12 CTLFireability.txt
-rw-r--r-- 1 mcc users 17K May 13 20:12 CTLFireability.xml
-rw-r--r-- 1 mcc users 2.9K May 14 10:05 LTLCardinality.txt
-rw-r--r-- 1 mcc users 21K May 14 10:05 LTLCardinality.xml
-rw-r--r-- 1 mcc users 1.9K May 14 10:05 LTLFireability.txt
-rw-r--r-- 1 mcc users 16K May 14 10:05 LTLFireability.xml
-rw-r--r-- 1 mcc users 1 May 12 20:42 NewModel
-rw-r--r-- 1 mcc users 3.3K May 13 14:39 ReachabilityCardinality.txt
-rw-r--r-- 1 mcc users 17K May 13 14:39 ReachabilityCardinality.xml
-rw-r--r-- 1 mcc users 3.0K May 13 09:29 ReachabilityFireability.txt
-rw-r--r-- 1 mcc users 20K May 13 09:29 ReachabilityFireability.xml
-rw-r--r-- 1 mcc users 1.6K May 13 16:53 UpperBounds.txt
-rw-r--r-- 1 mcc users 3.6K May 13 16:53 UpperBounds.xml
-rw-r--r-- 1 mcc users 6 May 12 20:42 equiv_col
-rw-r--r-- 1 mcc users 5 May 12 20:42 instance
-rw-r--r-- 1 mcc users 6 May 12 20:42 iscolored
-rw-r--r-- 1 mcc users 12K May 12 20:42 model.pnml
--------------------
content from stdout:
=== Data for post analysis generated by BenchKit (invocation template)
The expected result is a vector of booleans
BOOL_VECTOR
here is the order used to build the result vector(from text file)
FORMULA_NAME ShieldRVt-PT-004A-00
FORMULA_NAME ShieldRVt-PT-004A-01
FORMULA_NAME ShieldRVt-PT-004A-02
FORMULA_NAME ShieldRVt-PT-004A-03
FORMULA_NAME ShieldRVt-PT-004A-04
FORMULA_NAME ShieldRVt-PT-004A-05
FORMULA_NAME ShieldRVt-PT-004A-06
FORMULA_NAME ShieldRVt-PT-004A-07
FORMULA_NAME ShieldRVt-PT-004A-08
FORMULA_NAME ShieldRVt-PT-004A-09
FORMULA_NAME ShieldRVt-PT-004A-10
FORMULA_NAME ShieldRVt-PT-004A-11
FORMULA_NAME ShieldRVt-PT-004A-12
FORMULA_NAME ShieldRVt-PT-004A-13
FORMULA_NAME ShieldRVt-PT-004A-14
FORMULA_NAME ShieldRVt-PT-004A-15
=== Now, execution of the tool begins
BK_START 1590630400369
[2020-05-28 01:46:42] [INFO ] Running its-tools with arguments : [-pnfolder, /home/mcc/execution, -examination, LTLFireability, -z3path, /home/mcc/BenchKit//z3/bin/z3, -yices2path, /home/mcc/BenchKit//yices/bin/yices, -its, -ltsminpath, /home/mcc/BenchKit//lts_install_dir/, -greatspnpath, /home/mcc/BenchKit//greatspn/, -order, META, -manyOrder, -smt, -timeout, 3600]
[2020-05-28 01:46:42] [INFO ] Parsing pnml file : /home/mcc/execution/model.pnml
[2020-05-28 01:46:42] [INFO ] Load time of PNML (sax parser for PT used): 26 ms
[2020-05-28 01:46:42] [INFO ] Transformed 35 places.
[2020-05-28 01:46:42] [INFO ] Transformed 35 transitions.
[2020-05-28 01:46:42] [INFO ] Found NUPN structural information;
[2020-05-28 01:46:42] [INFO ] Parsed PT model containing 35 places and 35 transitions in 60 ms.
Ensure Unique test removed 1 transitions
Reduce redundant transitions removed 1 transitions.
Parsed 16 properties from file /home/mcc/execution/LTLFireability.xml in 14 ms.
Working with output stream class java.io.PrintStream
Incomplete random walk after 100000 steps, including 0 resets, run finished after 146 ms. (steps per millisecond=684 ) properties seen :[1, 1, 1, 1, 1, 1, 1, 1, 0, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1, 1]
// Phase 1: matrix 34 rows 35 cols
[2020-05-28 01:46:42] [INFO ] Computed 17 place invariants in 3 ms
[2020-05-28 01:46:42] [INFO ] [Real]Absence check using 17 positive place invariants in 16 ms returned unsat
Successfully simplified 1 atomic propositions for a total of 1 simplifications.
[2020-05-28 01:46:42] [INFO ] Initial state reduction rules for CTL removed 3 formulas.
[2020-05-28 01:46:42] [INFO ] Flatten gal took : 28 ms
FORMULA ShieldRVt-PT-004A-09 FALSE TECHNIQUES TOPOLOGICAL INITIAL_STATE
FORMULA ShieldRVt-PT-004A-08 TRUE TECHNIQUES TOPOLOGICAL INITIAL_STATE
FORMULA ShieldRVt-PT-004A-02 TRUE TECHNIQUES TOPOLOGICAL INITIAL_STATE
[2020-05-28 01:46:42] [INFO ] Flatten gal took : 6 ms
Using solver Z3 to compute partial order matrices.
Built C files in :
/home/mcc/execution
[2020-05-28 01:46:43] [INFO ] Applying decomposition
[2020-05-28 01:46:43] [INFO ] Flatten gal took : 5 ms
[2020-05-28 01:46:43] [INFO ] Input system was already deterministic with 34 transitions.
Converted graph to binary with : CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.louvain.binaries_1.0.0.202005100927/bin/convert-linux64, -i, /tmp/graph9818254141558695324.txt, -o, /tmp/graph9818254141558695324.bin, -w, /tmp/graph9818254141558695324.weights], workingDir=null]
Presburger conditions satisfied. Using coverability to approximate state space in K-Induction.
// Phase 1: matrix 34 rows 35 cols
[2020-05-28 01:46:43] [INFO ] Computed 17 place invariants in 1 ms
inv : p0 + p25 + p26 = 1
inv : p0 + p3 + p4 = 1
inv : p0 + p5 + p6 = 1
inv : p0 + p13 + p14 = 1
inv : p0 + p31 + p32 = 1
inv : p0 + p15 + p16 = 1
inv : p0 + p23 + p24 = 1
inv : p0 + p7 + p8 = 1
inv : p0 + p19 + p20 = 1
inv : p0 + p9 + p10 = 1
inv : p0 + p29 + p30 = 1
inv : p0 + p21 + p22 = 1
inv : p0 + p27 + p28 = 1
inv : p0 + p17 + p18 = 1
inv : p0 + p11 + p12 = 1
inv : p0 + p1 + p2 = 1
inv : p0 + p33 + p34 = 1
Total of 17 invariants.
[2020-05-28 01:46:43] [INFO ] Computed 17 place invariants in 2 ms
Built communities with : CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.louvain.binaries_1.0.0.202005100927/bin/louvain-linux64, /tmp/graph9818254141558695324.bin, -l, -1, -v, -w, /tmp/graph9818254141558695324.weights, -q, 0, -e, 0.001], workingDir=null]
[2020-05-28 01:46:43] [INFO ] Decomposing Gal with order
[2020-05-28 01:46:43] [INFO ] Rewriting arrays to variables to allow decomposition.
[2020-05-28 01:46:43] [INFO ] Removed a total of 12 redundant transitions.
[2020-05-28 01:46:43] [INFO ] Proved 35 variables to be positive in 116 ms
[2020-05-28 01:46:43] [INFO ] Computing symmetric may disable matrix : 34 transitions.
[2020-05-28 01:46:43] [INFO ] Computation of disable matrix completed :0/34 took 0 ms. Total solver calls (SAT/UNSAT): 0(0/0)
[2020-05-28 01:46:43] [INFO ] Computation of Complete disable matrix. took 1 ms. Total solver calls (SAT/UNSAT): 0(0/0)
[2020-05-28 01:46:43] [INFO ] Computing symmetric may enable matrix : 34 transitions.
[2020-05-28 01:46:43] [INFO ] Computation of Complete enable matrix. took 0 ms. Total solver calls (SAT/UNSAT): 0(0/0)
[2020-05-28 01:46:43] [INFO ] Flatten gal took : 59 ms
[2020-05-28 01:46:43] [INFO ] Fuse similar labels procedure discarded/fused a total of 0 labels/synchronizations in 2 ms.
[2020-05-28 01:46:43] [INFO ] Time to serialize gal into /home/mcc/execution/LTLFireability.pnml.gal : 4 ms
[2020-05-28 01:46:43] [INFO ] Time to serialize properties into /home/mcc/execution/LTLFireability.ltl : 1 ms
Invoking ITS tools like this :CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.202005100927/bin/its-ltl-linux64, --gc-threshold, 2000000, -i, /home/mcc/execution/LTLFireability.pnml.gal, -t, CGAL, -LTL, /home/mcc/execution/LTLFireability.ltl, -c, -stutter-deadlock], workingDir=/home/mcc/execution]
its-ltl command run as :
/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.202005100927/bin/its-ltl-linux64 --gc-threshold 2000000 -i /home/mcc/execution/LTLFireability.pnml.gal -t CGAL -LTL /home/mcc/execution/LTLFireability.ltl -c -stutter-deadlock
Read 13 LTL properties
Checking formula 0 : !((F((!(X(!(G(F("((i8.u15.p32==1)&&(i8.u16.p34==1))"))))))U(!(F("(((i8.u15.p32==1)&&(i8.u16.p34==1))||(((u7.p16==1)&&(i4.u8.p18==1))&&(u11.p23==1)))"))))))
Formula 0 simplified : !F(!X!GF"((i8.u15.p32==1)&&(i8.u16.p34==1))" U !F"(((i8.u15.p32==1)&&(i8.u16.p34==1))||(((u7.p16==1)&&(i4.u8.p18==1))&&(u11.p23==1)))")
built 10 ordering constraints for composite.
built 5 ordering constraints for composite.
built 8 ordering constraints for composite.
built 5 ordering constraints for composite.
built 5 ordering constraints for composite.
built 10 ordering constraints for composite.
Reverse transition relation is exact ! Faster fixpoint algorithm enabled.
2 unique states visited
2 strongly connected components in search stack
2 transitions explored
2 items max in DFS search stack
33 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.354231,30248,1,0,28790,61,430,58748,64,84,32205
an accepting run exists (use option '-e' to print it)
Formula 0 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-00 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 1 : !((X((X(F(G(F(X("(((u11.p24!=1)||(i6.u12.p26!=1))||(i8.u15.p31!=1))"))))))U(X("((i6.u10.p22==1)&&(i6.u12.p25==1))")))))
Formula 1 simplified : !X(XFGFX"(((u11.p24!=1)||(i6.u12.p26!=1))||(i8.u15.p31!=1))" U X"((i6.u10.p22==1)&&(i6.u12.p25==1))")
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.358878,31192,1,0,28820,61,493,58811,64,84,32439
an accepting run exists (use option '-e' to print it)
Formula 1 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-01 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 2 : !((F(!(F(F(G("(i6.u10.p21==1)")))))))
Formula 2 simplified : !F!FG"(i6.u10.p21==1)"
4 unique states visited
4 strongly connected components in search stack
5 transitions explored
4 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.362461,31424,1,0,29115,61,534,59152,65,84,33429
an accepting run exists (use option '-e' to print it)
Formula 2 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-03 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 3 : !(((X(X((!(F("(i4.u8.p17==1)")))||(!(X(!(F("((i8.u15.p32==1)&&(i8.u16.p34==1))"))))))))||(G("(i8.u13.p27==1)"))))
Formula 3 simplified : !(XX(!F"(i4.u8.p17==1)" | !X!F"((i8.u15.p32==1)&&(i8.u16.p34==1))") | G"(i8.u13.p27==1)")
6 unique states visited
6 strongly connected components in search stack
6 transitions explored
6 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.36586,31888,1,0,29273,61,584,59319,65,84,33901
an accepting run exists (use option '-e' to print it)
Formula 3 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-04 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 4 : !((G(!(X(X(X(X("(u5.p11==1)"))))))))
Formula 4 simplified : !G!XXXX"(u5.p11==1)"
7 unique states visited
7 strongly connected components in search stack
7 transitions explored
7 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.368695,32084,1,0,29489,61,610,59562,65,84,34462
an accepting run exists (use option '-e' to print it)
Formula 4 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-05 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 5 : !((G(X((G(("(((u5.p11==1)&&(u9.p20==1))&&(i6.u12.p26==1))")U("(u7.p15==1)")))U(X(X((G(X("(u7.p15==1)")))||("(u9.p19==1)"))))))))
Formula 5 simplified : !GX(G("(((u5.p11==1)&&(u9.p20==1))&&(i6.u12.p26==1))" U "(u7.p15==1)") U XX("(u9.p19==1)" | GX"(u7.p15==1)"))
8 unique states visited
8 strongly connected components in search stack
10 transitions explored
8 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.38352,33208,1,0,30102,61,673,60244,67,84,35524
an accepting run exists (use option '-e' to print it)
Formula 5 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-06 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 6 : !((!(X((F(!(G("((i8.u14.p30==1)&&(i8.u16.p33==1))"))))||(G((X(G("(((u5.p12==1)&&(i4.u6.p13==1))&&(u7.p16==1))")))||("(i1.u4.p9==1)")))))))
Formula 6 simplified : X(F!G"((i8.u14.p30==1)&&(i8.u16.p33==1))" | G("(i1.u4.p9==1)" | XG"(((u5.p12==1)&&(i4.u6.p13==1))&&(u7.p16==1))"))
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.384891,33208,1,0,30102,61,693,60246,67,84,35552
an accepting run exists (use option '-e' to print it)
Formula 6 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-07 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 7 : !((X((X("(((i1.u2.p6==1)&&(i1.u4.p9==1))&&(((i0.u1.p4!=1)||(i1.u2.p5!=1))||(i0.u3.p8!=1)))"))&&(X(F(("((i1.u2.p6==1)&&(i1.u4.p9==1))")U("((((i0.u1.p4==1)&&(i1.u2.p5==1))&&(i0.u3.p8==1))||(i8.u13.p27==1))")))))))
Formula 7 simplified : !X(X"(((i1.u2.p6==1)&&(i1.u4.p9==1))&&(((i0.u1.p4!=1)||(i1.u2.p5!=1))||(i0.u3.p8!=1)))" & XF("((i1.u2.p6==1)&&(i1.u4.p9==1))" U "((((i0.u1.p4==1)&&(i1.u2.p5==1))&&(i0.u3.p8==1))||(i8.u13.p27==1))"))
5 unique states visited
5 strongly connected components in search stack
5 transitions explored
5 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.38612,33208,1,0,30103,61,730,60250,68,84,35615
an accepting run exists (use option '-e' to print it)
Formula 7 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-10 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 8 : !((X((!(X(X(G("(((u5.p12==1)&&(i4.u6.p13==1))&&(u7.p16==1))")))))||(!(F("(((i0.u0.p2==1)&&(i0.u1.p4==1))&&(i1.u4.p10==1))"))))))
Formula 8 simplified : !X(!XXG"(((u5.p12==1)&&(i4.u6.p13==1))&&(u7.p16==1))" | !F"(((i0.u0.p2==1)&&(i0.u1.p4==1))&&(i1.u4.p10==1))")
4 unique states visited
0 strongly connected components in search stack
3 transitions explored
4 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.387214,33208,1,0,30103,61,787,60250,69,84,35672
no accepting run found
Formula 8 is TRUE no accepting run found.
FORMULA ShieldRVt-PT-004A-11 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 9 : !((F(G((((!(X((((G("(u9.p19==1)"))&&("(u5.p12==1)"))&&("(i4.u6.p13==1)"))&&("(u7.p16==1)"))))&&("(u5.p12==1)"))&&("(i4.u6.p13==1)"))&&("(u7.p16==1)")))))
Formula 9 simplified : !FG("(i4.u6.p13==1)" & "(u5.p12==1)" & "(u7.p16==1)" & !X("(i4.u6.p13==1)" & "(u5.p12==1)" & "(u7.p16==1)" & G"(u9.p19==1)"))
2 unique states visited
2 strongly connected components in search stack
2 transitions explored
2 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.389568,33208,1,0,30203,61,832,60330,69,84,35927
an accepting run exists (use option '-e' to print it)
Formula 9 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-12 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 10 : !((G(F(G("((i8.u14.p30==1)&&(i8.u16.p33==1))")))))
Formula 10 simplified : !GFG"((i8.u14.p30==1)&&(i8.u16.p33==1))"
2 unique states visited
2 strongly connected components in search stack
2 transitions explored
2 items max in DFS search stack
11 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.504876,37960,1,0,40996,61,847,81025,69,84,47488
an accepting run exists (use option '-e' to print it)
Formula 10 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-13 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 11 : !((F(("(i4.u8.p17==1)")U((F("(((u5.p11==1)&&(u9.p20==1))&&(i6.u12.p26==1))"))&&(F((((F(("(i4.u8.p17==1)")U("(i0.u1.p3==1)")))&&("(i0.u1.p3==1)"))&&("(u5.p12==1)"))&&("(i4.u8.p18==1)")))))))
Formula 11 simplified : !F("(i4.u8.p17==1)" U (F"(((u5.p11==1)&&(u9.p20==1))&&(i6.u12.p26==1))" & F("(i0.u1.p3==1)" & "(i4.u8.p18==1)" & "(u5.p12==1)" & F("(i4.u8.p17==1)" U "(i0.u1.p3==1)"))))
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
6 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.559183,40600,1,0,48350,61,939,88293,69,84,58689
an accepting run exists (use option '-e' to print it)
Formula 11 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-14 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 12 : !((X(G((((!((!(("(((i0.u3.p8==1)&&(i1.u4.p10==1))&&(u7.p15==1))")U("(u9.p19==1)")))U(X("(u9.p19==1)"))))&&(G("((i8.u15.p32==1)&&(i8.u16.p34==1))")))&&("(i8.u15.p32==1)"))&&("(i8.u16.p34==1)")))))
Formula 12 simplified : !XG("(i8.u15.p32==1)" & "(i8.u16.p34==1)" & !(!("(((i0.u3.p8==1)&&(i1.u4.p10==1))&&(u7.p15==1))" U "(u9.p19==1)") U X"(u9.p19==1)") & G"((i8.u15.p32==1)&&(i8.u16.p34==1))")
5 unique states visited
5 strongly connected components in search stack
5 transitions explored
5 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.562956,41128,1,0,48350,61,981,88293,69,84,58729
an accepting run exists (use option '-e' to print it)
Formula 12 is FALSE accepting run found.
FORMULA ShieldRVt-PT-004A-15 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Skipping mayMatrices nes/nds SMT solver raised an error :unknown
java.lang.RuntimeException: SMT solver raised an error :unknown
at fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver.computeAblingForPredicate(NecessaryEnablingsolver.java:768)
at fr.lip6.move.gal.gal2pins.Gal2PinsTransformerNext.printLabels(Gal2PinsTransformerNext.java:512)
at fr.lip6.move.gal.gal2pins.Gal2PinsTransformerNext.printDependencyMatrix(Gal2PinsTransformerNext.java:209)
at fr.lip6.move.gal.gal2pins.Gal2PinsTransformerNext.buildBodyFile(Gal2PinsTransformerNext.java:85)
at fr.lip6.move.gal.gal2pins.Gal2PinsTransformerNext.transform(Gal2PinsTransformerNext.java:831)
at fr.lip6.move.gal.application.LTSminRunner$1.run(LTSminRunner.java:73)
at java.base/java.lang.Thread.run(Thread.java:834)
[2020-05-28 01:46:44] [INFO ] Built C files in 1013ms conformant to PINS in folder :/home/mcc/execution
Running compilation step : CommandLine [args=[gcc, -c, -I/home/mcc/BenchKit//lts_install_dir//include, -I., -std=c99, -fPIC, -O2, model.c], workingDir=/home/mcc/execution]
WARNING : LTS min runner thread was asked to interrupt. Dying gracefully.
BK_STOP 1590630404515
--------------------
content from stderr:
+ export BINDIR=/home/mcc/BenchKit/
+ BINDIR=/home/mcc/BenchKit/
++ pwd
+ export MODEL=/home/mcc/execution
+ MODEL=/home/mcc/execution
+ [[ LTLFireability = StateSpace ]]
+ /home/mcc/BenchKit//runeclipse.sh /home/mcc/execution LTLFireability -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -greatspnpath /home/mcc/BenchKit//greatspn/ -order META -manyOrder -smt -timeout 3600
+ ulimit -s 65536
+ [[ -z '' ]]
+ export LTSMIN_MEM_SIZE=8589934592
+ LTSMIN_MEM_SIZE=8589934592
+ /home/mcc/BenchKit//itstools/its-tools -data /home/mcc/execution/workspace -pnfolder /home/mcc/execution -examination LTLFireability -z3path /home/mcc/BenchKit//z3/bin/z3 -yices2path /home/mcc/BenchKit//yices/bin/yices -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -greatspnpath /home/mcc/BenchKit//greatspn/ -order META -manyOrder -smt -timeout 3600 -vmargs -Dosgi.locking=none -Declipse.stateSaveDelayInterval=-1 -Dosgi.configuration.area=/tmp/.eclipse -Xss128m -Xms40m -Xmx16000m -Dfile.encoding=UTF-8 -Dosgi.requiredJavaVersion=1.6
Sequence of Actions to be Executed by the VM
This is useful if one wants to reexecute the tool in the VM from the submitted image disk.
set -x
# this is for BenchKit: configuration of major elements for the test
export BK_INPUT="ShieldRVt-PT-004A"
export BK_EXAMINATION="LTLFireability"
export BK_TOOL="itstools"
export BK_RESULT_DIR="/tmp/BK_RESULTS/OUTPUTS"
export BK_TIME_CONFINEMENT="3600"
export BK_MEMORY_CONFINEMENT="16384"
# this is specific to your benchmark or test
export BIN_DIR="$HOME/BenchKit/bin"
# remove the execution directoty if it exists (to avoid increse of .vmdk images)
if [ -d execution ] ; then
rm -rf execution
fi
# this is for BenchKit: explicit launching of the test
echo "====================================================================="
echo " Generated by BenchKit 2-4028"
echo " Executing tool itstools"
echo " Input is ShieldRVt-PT-004A, examination is LTLFireability"
echo " Time confinement is $BK_TIME_CONFINEMENT seconds"
echo " Memory confinement is 16384 MBytes"
echo " Number of cores is 4"
echo " Run identifier is r210-tajo-159033476500970"
echo "====================================================================="
echo
echo "--------------------"
echo "preparation of the directory to be used:"
tar xzf /home/mcc/BenchKit/INPUTS/ShieldRVt-PT-004A.tgz
mv ShieldRVt-PT-004A execution
cd execution
if [ "LTLFireability" = "ReachabilityDeadlock" ] || [ "LTLFireability" = "UpperBounds" ] || [ "LTLFireability" = "QuasiLiveness" ] || [ "LTLFireability" = "StableMarking" ] || [ "LTLFireability" = "Liveness" ] || [ "LTLFireability" = "OneSafe" ] || [ "LTLFireability" = "StateSpace" ]; then
rm -f GenericPropertiesVerdict.xml
fi
pwd
ls -lh
echo
echo "--------------------"
echo "content from stdout:"
echo
echo "=== Data for post analysis generated by BenchKit (invocation template)"
echo
if [ "LTLFireability" = "UpperBounds" ] ; then
echo "The expected result is a vector of positive values"
echo NUM_VECTOR
elif [ "LTLFireability" != "StateSpace" ] ; then
echo "The expected result is a vector of booleans"
echo BOOL_VECTOR
else
echo "no data necessary for post analysis"
fi
echo
if [ -f "LTLFireability.txt" ] ; then
echo "here is the order used to build the result vector(from text file)"
for x in $(grep Property LTLFireability.txt | cut -d ' ' -f 2 | sort -u) ; do
echo "FORMULA_NAME $x"
done
elif [ -f "LTLFireability.xml" ] ; then # for cunf (txt files deleted;-)
echo echo "here is the order used to build the result vector(from xml file)"
for x in $(grep '
echo "FORMULA_NAME $x"
done
elif [ "LTLFireability" = "ReachabilityDeadlock" ] || [ "LTLFireability" = "QuasiLiveness" ] || [ "LTLFireability" = "StableMarking" ] || [ "LTLFireability" = "Liveness" ] || [ "LTLFireability" = "OneSafe" ] ; then
echo "FORMULA_NAME LTLFireability"
fi
echo
echo "=== Now, execution of the tool begins"
echo
echo -n "BK_START "
date -u +%s%3N
echo
timeout -s 9 $BK_TIME_CONFINEMENT bash -c "/home/mcc/BenchKit/BenchKit_head.sh 2> STDERR ; echo ; echo -n \"BK_STOP \" ; date -u +%s%3N"
if [ $? -eq 137 ] ; then
echo
echo "BK_TIME_CONFINEMENT_REACHED"
fi
echo
echo "--------------------"
echo "content from stderr:"
echo
cat STDERR ;