About the Execution of ITS-Tools.L for TCPcondis-PT-05
| Execution Summary | |||||
| Max Memory Used (MB) |
Time wait (ms) | CPU Usage (ms) | I/O Wait (ms) | Computed Result | Execution Status |
| 15752.080 | 287538.00 | 290387.00 | 889.60 | FFFFTTTFFFTTTTTT | normal |
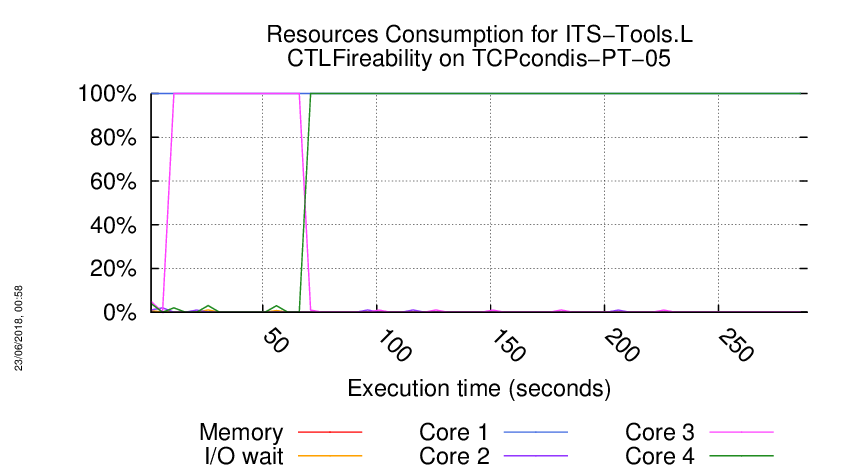
Execution Chart
We display below the execution chart for this examination (boot time has been removed).
Trace from the execution
Waiting for the VM to be ready (probing ssh)
...................
/home/mcc/execution
total 196K
-rw-r--r-- 1 mcc users 2.9K May 15 18:54 CTLCardinality.txt
-rw-r--r-- 1 mcc users 15K May 15 18:54 CTLCardinality.xml
-rw-r--r-- 1 mcc users 2.5K May 15 18:54 CTLFireability.txt
-rw-r--r-- 1 mcc users 17K May 15 18:54 CTLFireability.xml
-rw-r--r-- 1 mcc users 4.0K May 15 18:50 GenericPropertiesDefinition.xml
-rw-r--r-- 1 mcc users 6.0K May 15 18:50 GenericPropertiesVerdict.xml
-rw-r--r-- 1 mcc users 2.3K May 26 09:27 LTLCardinality.txt
-rw-r--r-- 1 mcc users 9.9K May 26 09:27 LTLCardinality.xml
-rw-r--r-- 1 mcc users 1.8K May 26 09:27 LTLFireability.txt
-rw-r--r-- 1 mcc users 8.3K May 26 09:27 LTLFireability.xml
-rw-r--r-- 1 mcc users 4.2K May 15 18:54 ReachabilityCardinality.txt
-rw-r--r-- 1 mcc users 22K May 15 18:54 ReachabilityCardinality.xml
-rw-r--r-- 1 mcc users 106 May 15 18:54 ReachabilityDeadlock.txt
-rw-r--r-- 1 mcc users 344 May 15 18:54 ReachabilityDeadlock.xml
-rw-r--r-- 1 mcc users 2.9K May 15 18:54 ReachabilityFireability.txt
-rw-r--r-- 1 mcc users 19K May 15 18:54 ReachabilityFireability.xml
-rw-r--r-- 1 mcc users 1.7K May 15 18:54 UpperBounds.txt
-rw-r--r-- 1 mcc users 3.7K May 15 18:54 UpperBounds.xml
-rw-r--r-- 1 mcc users 6 May 15 18:50 equiv_col
-rw-r--r-- 1 mcc users 3 May 15 18:50 instance
-rw-r--r-- 1 mcc users 6 May 15 18:50 iscolored
-rwxr-xr-x 1 mcc users 24K May 15 18:50 model.pnml
=====================================================================
Generated by BenchKit 2-3637
Executing tool itstoolsl
Input is TCPcondis-PT-05, examination is CTLFireability
Time confinement is 3600 seconds
Memory confinement is 16384 MBytes
Number of cores is 4
Run identifier is r177-smll-152708747600179
=====================================================================
--------------------
content from stdout:
=== Data for post analysis generated by BenchKit (invocation template)
The expected result is a vector of booleans
BOOL_VECTOR
here is the order used to build the result vector(from text file)
FORMULA_NAME TCPcondis-PT-05-CTLFireability-00
FORMULA_NAME TCPcondis-PT-05-CTLFireability-01
FORMULA_NAME TCPcondis-PT-05-CTLFireability-02
FORMULA_NAME TCPcondis-PT-05-CTLFireability-03
FORMULA_NAME TCPcondis-PT-05-CTLFireability-04
FORMULA_NAME TCPcondis-PT-05-CTLFireability-05
FORMULA_NAME TCPcondis-PT-05-CTLFireability-06
FORMULA_NAME TCPcondis-PT-05-CTLFireability-07
FORMULA_NAME TCPcondis-PT-05-CTLFireability-08
FORMULA_NAME TCPcondis-PT-05-CTLFireability-09
FORMULA_NAME TCPcondis-PT-05-CTLFireability-10
FORMULA_NAME TCPcondis-PT-05-CTLFireability-11
FORMULA_NAME TCPcondis-PT-05-CTLFireability-12
FORMULA_NAME TCPcondis-PT-05-CTLFireability-13
FORMULA_NAME TCPcondis-PT-05-CTLFireability-14
FORMULA_NAME TCPcondis-PT-05-CTLFireability-15
=== Now, execution of the tool begins
BK_START 1527453972452
Converted graph to binary with : CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.louvain.binaries_1.0.0.201805241334/bin/convert-linux64, -i, /tmp/graph1947020342883966543.txt, -o, /tmp/graph1947020342883966543.bin, -w, /tmp/graph1947020342883966543.weights], workingDir=null]
Built communities with : CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.louvain.binaries_1.0.0.201805241334/bin/louvain-linux64, /tmp/graph1947020342883966543.bin, -l, -1, -v, -w, /tmp/graph1947020342883966543.weights, -q, 0, -e, 0.001], workingDir=null]
Invoking ITS tools like this :CommandLine [args=[/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.201805241334/bin/its-ctl-linux64, --gc-threshold, 2000000, --quiet, -i, /home/mcc/execution/CTLFireability.pnml.gal, -t, CGAL, -ctl, /home/mcc/execution/CTLFireability.ctl], workingDir=/home/mcc/execution]
its-ctl command run as :
/home/mcc/BenchKit/itstools/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.201805241334/bin/its-ctl-linux64 --gc-threshold 2000000 --quiet -i /home/mcc/execution/CTLFireability.pnml.gal -t CGAL -ctl /home/mcc/execution/CTLFireability.ctl
No direction supplied, using forward translation only.
Parsed 16 CTL formulae.
built 10 ordering constraints for composite.
built 17 ordering constraints for composite.
built 12 ordering constraints for composite.
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
reachable,2.98583e+06,1.52827,38832,5754,517,81280,4274,136,68035,51,50873,0
Converting to forward existential form...Done !
original formula: AF((((((i1.u1.CLOSEWAIT>=1)||(i0.u5.xESTAB>=1))&&((u7.xLISTEN>=1)&&((i1.u1.LASTACK>=1)&&(u3.xFINACK>=1)))) + AX(((u7.xCLOSING>=1)&&(i0.u0.FINACK>=1)))) + !((u7.xCLOSED>=1))))
=> equivalent forward existential formula: [FwdG(Init,!((((((i1.u1.CLOSEWAIT>=1)||(i0.u5.xESTAB>=1))&&((u7.xLISTEN>=1)&&((i1.u1.LASTACK>=1)&&(u3.xFINACK>=1)))) + !(EX(!(((u7.xCLOSING>=1)&&(i0.u0.FINACK>=1)))))) + !((u7.xCLOSED>=1)))))] = FALSE
Reverse transition relation is NOT exact ! Due to transitions raf2, xraf2, Intersection with reachable at each step enabled. (destroyed/reverse/intersect/total) :0/30/2/32
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
(forward)formula 0,0,44.5833,493980,1,0,941127,63499,599,1.32615e+06,276,1.09164e+06,901563
FORMULA TCPcondis-PT-05-CTLFireability-00 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: AF(((((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))&&(!(((u3.CLOSING>=1)&&(u3.xFINACK>=1))&&((u2.SYNSENT>=1)&&(u7.xSYN>=1))))) + ((u2.CLOSED>=1) * EX(((i0.u6.xFINWAIT1>=1)&&(i0.u0.FINACK>=1))))))
=> equivalent forward existential formula: [FwdG(Init,!(((((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))&&(!(((u3.CLOSING>=1)&&(u3.xFINACK>=1))&&((u2.SYNSENT>=1)&&(u7.xSYN>=1))))) + ((u2.CLOSED>=1) * EX(((i0.u6.xFINWAIT1>=1)&&(i0.u0.FINACK>=1)))))))] = FALSE
(forward)formula 1,0,74.5147,885376,1,0,1.5638e+06,86786,630,2.43317e+06,277,1.92189e+06,1436375
FORMULA TCPcondis-PT-05-CTLFireability-01 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: AF((((u2.SYNSENT>=1)&&(u7.xSYN>=1)) + AF(((i0.u5.xESTAB>=1)&&(i1.u1.FIN>=1)))))
=> equivalent forward existential formula: [FwdG(Init,!((((u2.SYNSENT>=1)&&(u7.xSYN>=1)) + !(EG(!(((i0.u5.xESTAB>=1)&&(i1.u1.FIN>=1))))))))] = FALSE
(forward)formula 2,0,111.732,1235304,1,0,2.05698e+06,102846,659,3.29057e+06,280,2.5254e+06,1833288
FORMULA TCPcondis-PT-05-CTLFireability-02 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: (EX((((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1))||((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1)))) + AF(EG(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1)))))
=> equivalent forward existential formula: [FwdG((Init * !(EX((((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1))||((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1)))))),!(EG(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1)))))] = FALSE
(forward)formula 3,0,138.824,1439256,1,0,2.38498e+06,110229,691,3.85753e+06,282,2.93261e+06,2122916
FORMULA TCPcondis-PT-05-CTLFireability-03 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: EG((!(EG(((u2.LISTEN>=1)&&(u7.xSYN>=1)))) + (u7.xCLOSED>=1)))
=> equivalent forward existential formula: [FwdG(Init,(!(EG(((u2.LISTEN>=1)&&(u7.xSYN>=1)))) + (u7.xCLOSED>=1)))] != FALSE
(forward)formula 4,1,151.232,1521360,1,0,2.47835e+06,116879,714,4.10017e+06,283,3.17816e+06,2172246
FORMULA TCPcondis-PT-05-CTLFireability-04 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: EF(((((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))&&((u3.FINWAIT1>=1)&&(i0.u0.xFIN>=1)))&&(!((u3.FINWAIT1>=1)&&(u3.xFINACK>=1)))))
=> equivalent forward existential formula: [(FwdU(Init,TRUE) * ((((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))&&((u3.FINWAIT1>=1)&&(i0.u0.xFIN>=1)))&&(!((u3.FINWAIT1>=1)&&(u3.xFINACK>=1)))))] != FALSE
(forward)formula 5,1,151.255,1521888,1,0,2.47906e+06,116879,736,4.10045e+06,291,3.17817e+06,2175266
FORMULA TCPcondis-PT-05-CTLFireability-05 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: EG(EX((u7.xCLOSED>=1)))
=> equivalent forward existential formula: [FwdG(Init,EX((u7.xCLOSED>=1)))] != FALSE
(forward)formula 6,1,161.201,1608480,1,0,2.65858e+06,118919,739,4.23533e+06,291,3.22759e+06,2321297
FORMULA TCPcondis-PT-05-CTLFireability-06 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: !(((EF((((u7.xSYNSENT>=1)&&(u2.SYN>=1))&&((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1)))) + AX(((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1)))) * EF(((i0.u5.SYNACK>=1)&&(i0.u5.xSYNRCVD>=1)))))
=> equivalent forward existential formula: ([(EY((Init * !(E(TRUE U (((u7.xSYNSENT>=1)&&(u2.SYN>=1))&&((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))))))) * !(((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1))))] != FALSE + [(Init * !(E(TRUE U ((i0.u5.SYNACK>=1)&&(i0.u5.xSYNRCVD>=1)))))] != FALSE)
(forward)formula 7,0,162.858,1633032,1,0,2.71016e+06,119058,837,4.28179e+06,303,3.2355e+06,2436454
FORMULA TCPcondis-PT-05-CTLFireability-07 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: (E((u2.CLOSED>=1) U AG(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1)))) + ((i0.u6.xFINWAIT1>=1)&&(i1.u1.FIN>=1)))
=> equivalent forward existential formula: ([(FwdU(Init,(u2.CLOSED>=1)) * !(E(TRUE U !(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1))))))] != FALSE + [(Init * ((i0.u6.xFINWAIT1>=1)&&(i1.u1.FIN>=1)))] != FALSE)
(forward)formula 8,0,163.805,1643064,1,0,2.72694e+06,119131,840,4.30516e+06,303,3.24588e+06,2468829
FORMULA TCPcondis-PT-05-CTLFireability-08 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: !(((!(EX((u7.xLISTEN>=1))) + EG(((u7.xCLOSED>=1)||((u3.CLOSING>=1)&&(u3.xFINACK>=1))))) * EF(((i1.u1.CLOSEWAIT>=1)||((u7.xSYNSENT>=1)&&(u2.SYN>=1))))))
=> equivalent forward existential formula: ([(EY((Init * !(EG(((u7.xCLOSED>=1)||((u3.CLOSING>=1)&&(u3.xFINACK>=1))))))) * (u7.xLISTEN>=1))] != FALSE + [(Init * !(E(TRUE U ((i1.u1.CLOSEWAIT>=1)||((u7.xSYNSENT>=1)&&(u2.SYN>=1))))))] != FALSE)
(forward)formula 9,0,164.893,1659168,1,0,2.75255e+06,121449,856,4.35222e+06,303,3.28258e+06,2502074
FORMULA TCPcondis-PT-05-CTLFireability-09 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is FALSE !
***************************************
original formula: AG(AF(EF(((u3.CLOSING>=1)&&(u3.xFINACK>=1)))))
=> equivalent forward existential formula: [FwdG(FwdU(Init,TRUE),!(E(TRUE U ((u3.CLOSING>=1)&&(u3.xFINACK>=1)))))] = FALSE
(forward)formula 10,1,166.874,1678176,1,0,2.77938e+06,121491,859,4.38068e+06,303,3.29121e+06,2547499
FORMULA TCPcondis-PT-05-CTLFireability-10 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: A(((u2.LISTEN>=1) * EF((i0.u4.xCLOSEWAIT>=1))) U EG(!((((i1.u8.xSYNACK>=1)&&(u2.SYNSENT>=1))&&(u7.xSYN>=1)))))
=> equivalent forward existential formula: [((Init * !(EG(!(EG(!((((i1.u8.xSYNACK>=1)&&(u2.SYNSENT>=1))&&(u7.xSYN>=1)))))))) * !(E(!(EG(!((((i1.u8.xSYNACK>=1)&&(u2.SYNSENT>=1))&&(u7.xSYN>=1))))) U (!(((u2.LISTEN>=1) * E(TRUE U (i0.u4.xCLOSEWAIT>=1)))) * !(EG(!((((i1.u8.xSYNACK>=1)&&(u2.SYNSENT>=1))&&(u7.xSYN>=1)))))))))] != FALSE
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
Using saturation style SCC detection
(forward)formula 11,1,171.164,1756848,1,0,2.96056e+06,123973,913,4.5105e+06,316,3.31688e+06,2754500
FORMULA TCPcondis-PT-05-CTLFireability-11 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: AG((((((u2.LISTEN>=1)&&(u7.xCLOSED>=1))&&((((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1))||((u2.SYNSENT>=1)&&(u7.xSYN>=1)))) + EF(((i0.u5.SYNACK>=1)&&(i0.u5.xSYNRCVD>=1)))) + (EF((u2.LISTEN>=1)) * ((i0.u4.xCLOSEWAIT>=1)||(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1))||((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1)))))))
=> equivalent forward existential formula: [(((FwdU(Init,TRUE) * !((E(TRUE U (u2.LISTEN>=1)) * ((i0.u4.xCLOSEWAIT>=1)||(((u3.FINWAIT2>=1)&&(i0.u0.xFIN>=1))||((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))))))) * !((((u2.LISTEN>=1)&&(u7.xCLOSED>=1))&&((((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1))||((u2.SYNSENT>=1)&&(u7.xSYN>=1)))))) * !(E(TRUE U ((i0.u5.SYNACK>=1)&&(i0.u5.xSYNRCVD>=1)))))] = FALSE
(forward)formula 12,1,171.165,1757112,1,0,2.96056e+06,123973,913,4.5105e+06,316,3.31688e+06,2754500
FORMULA TCPcondis-PT-05-CTLFireability-12 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: E(!((((i1.u1.LASTACK>=1)&&(u3.xFINACK>=1))||((((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1))||((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1))))) U (AF(((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1))) * AF((i0.u5.xESTAB>=1))))
=> equivalent forward existential formula: [((FwdU(Init,!((((i1.u1.LASTACK>=1)&&(u3.xFINACK>=1))||((((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1))||((i0.u6.xFINWAIT2>=1)&&(i1.u1.FIN>=1)))))) * !(EG(!(((i0.u4.xLASTACK>=1)&&(i0.u0.FINACK>=1)))))) * !(EG(!((i0.u5.xESTAB>=1)))))] != FALSE
(forward)formula 13,1,271.434,2200748,1,0,3.70135e+06,129669,441,5.15512e+06,160,3.61226e+06,830931
FORMULA TCPcondis-PT-05-CTLFireability-13 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: (E(!(((u7.xTIMEWAIT>=1)&&((u3.CLOSING>=1)&&(u3.xFINACK>=1)))) U ((((u3.CLOSING>=1)&&(u3.xFINACK>=1))||((u3.FINWAIT1>=1)&&(u3.xFINACK>=1)))&&(((u3.FINWAIT1>=1)&&(i0.u0.xFIN>=1))&&(((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1))))) + EX((i1.u1.CLOSEWAIT>=1)))
=> equivalent forward existential formula: ([(FwdU(Init,!(((u7.xTIMEWAIT>=1)&&((u3.CLOSING>=1)&&(u3.xFINACK>=1))))) * ((((u3.CLOSING>=1)&&(u3.xFINACK>=1))||((u3.FINWAIT1>=1)&&(u3.xFINACK>=1)))&&(((u3.FINWAIT1>=1)&&(i0.u0.xFIN>=1))&&(((i0.u5.SYNACK>=1)&&(u7.xSYNSENT>=1))&&(u2.SYN>=1)))))] != FALSE + [(EY(Init) * (i1.u1.CLOSEWAIT>=1))] != FALSE)
(forward)formula 14,1,281.584,2200748,1,0,3.70135e+06,129669,532,5.15512e+06,177,3.61226e+06,1061804
FORMULA TCPcondis-PT-05-CTLFireability-14 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
original formula: EF(EG((((i0.u5.xESTAB>=1)||(u2.CLOSED>=1))&&(!((i0.u5.xESTAB>=1)&&(i1.u1.FIN>=1))))))
=> equivalent forward existential formula: [FwdG(FwdU(Init,TRUE),(((i0.u5.xESTAB>=1)||(u2.CLOSED>=1))&&(!((i0.u5.xESTAB>=1)&&(i1.u1.FIN>=1)))))] != FALSE
(forward)formula 15,1,283.431,2200748,1,0,3.70135e+06,129669,570,5.15512e+06,183,3.61226e+06,1170151
FORMULA TCPcondis-PT-05-CTLFireability-15 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Formula is TRUE !
***************************************
ITS tools runner thread asked to quit. Dying gracefully.
BK_STOP 1527454259990
--------------------
content from stderr:
+ export BINDIR=/home/mcc/BenchKit/
+ BINDIR=/home/mcc/BenchKit/
++ pwd
+ export MODEL=/home/mcc/execution
+ MODEL=/home/mcc/execution
+ /home/mcc/BenchKit//runeclipse.sh /home/mcc/execution CTLFireability -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -louvain -smt
+ ulimit -s 65536
+ [[ -z '' ]]
+ export LTSMIN_MEM_SIZE=8589934592
+ LTSMIN_MEM_SIZE=8589934592
+ /home/mcc/BenchKit//itstools/its-tools -consoleLog -data /home/mcc/execution/workspace -pnfolder /home/mcc/execution -examination CTLFireability -z3path /home/mcc/BenchKit//z3/bin/z3 -yices2path /home/mcc/BenchKit//yices/bin/yices -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -louvain -smt -vmargs -Dosgi.locking=none -Declipse.stateSaveDelayInterval=-1 -Dosgi.configuration.area=/tmp/.eclipse -Xss8m -Xms40m -Xmx8192m -Dfile.encoding=UTF-8 -Dosgi.requiredJavaVersion=1.6
May 27, 2018 8:46:14 PM fr.lip6.move.gal.application.Application start
INFO: Running its-tools with arguments : [-pnfolder, /home/mcc/execution, -examination, CTLFireability, -z3path, /home/mcc/BenchKit//z3/bin/z3, -yices2path, /home/mcc/BenchKit//yices/bin/yices, -its, -ltsminpath, /home/mcc/BenchKit//lts_install_dir/, -louvain, -smt]
May 27, 2018 8:46:14 PM fr.lip6.move.gal.application.MccTranslator transformPNML
INFO: Parsing pnml file : /home/mcc/execution/model.pnml
May 27, 2018 8:46:14 PM fr.lip6.move.gal.nupn.PTNetHandler startElement
WARNING: Skipping unknown tool specific annotation : Tina
May 27, 2018 8:46:14 PM fr.lip6.move.gal.nupn.PTNetHandler startElement
WARNING: Unknown XML tag in source file: size
May 27, 2018 8:46:14 PM fr.lip6.move.gal.nupn.PTNetHandler startElement
WARNING: Unknown XML tag in source file: color
May 27, 2018 8:46:14 PM fr.lip6.move.gal.nupn.PTNetReader loadFromXML
INFO: Load time of PNML (sax parser for PT used): 49 ms
May 27, 2018 8:46:14 PM fr.lip6.move.gal.pnml.togal.PTGALTransformer handlePage
INFO: Transformed 30 places.
May 27, 2018 8:46:14 PM fr.lip6.move.gal.pnml.togal.PTGALTransformer handlePage
INFO: Transformed 32 transitions.
May 27, 2018 8:46:14 PM fr.lip6.move.serialization.SerializationUtil systemToFile
INFO: Time to serialize gal into /home/mcc/execution/model.pnml.img.gal : 10 ms
May 27, 2018 8:46:14 PM fr.lip6.move.gal.application.MccTranslator applyOrder
INFO: Applying decomposition
May 27, 2018 8:46:14 PM fr.lip6.move.gal.instantiate.GALRewriter flatten
INFO: Flatten gal took : 31 ms
May 27, 2018 8:46:14 PM fr.lip6.move.gal.instantiate.GALRewriter flatten
INFO: Flatten gal took : 15 ms
Begin: Sun May 27 20:46:15 2018
Computation of communities with the Newman-Girvan Modularity quality function
level 0:
start computation: Sun May 27 20:46:15 2018
network size: 30 nodes, 148 links, 64 weight
quality increased from -0.038303 to 0.341024
end computation: Sun May 27 20:46:15 2018
level 1:
start computation: Sun May 27 20:46:15 2018
network size: 9 nodes, 61 links, 64 weight
quality increased from 0.341024 to 0.36556
end computation: Sun May 27 20:46:15 2018
level 2:
start computation: Sun May 27 20:46:15 2018
network size: 5 nodes, 23 links, 64 weight
quality increased from 0.36556 to 0.36556
end computation: Sun May 27 20:46:15 2018
End: Sun May 27 20:46:15 2018
Total duration: 0 sec
0.36556
May 27, 2018 8:46:15 PM fr.lip6.move.gal.instantiate.CompositeBuilder decomposeWithOrder
INFO: Decomposing Gal with order
May 27, 2018 8:46:15 PM fr.lip6.move.gal.instantiate.GALRewriter flatten
INFO: Flatten gal took : 13 ms
May 27, 2018 8:46:15 PM fr.lip6.move.gal.instantiate.CompositeBuilder rewriteArraysToAllowPartition
INFO: Rewriting arrays to variables to allow decomposition.
May 27, 2018 8:46:15 PM fr.lip6.move.gal.instantiate.Instantiator fuseIsomorphicEffects
INFO: Removed a total of 24 redundant transitions.
May 27, 2018 8:46:15 PM fr.lip6.move.serialization.SerializationUtil systemToFile
INFO: Time to serialize gal into /home/mcc/execution/CTLFireability.pnml.gal : 3 ms
May 27, 2018 8:46:15 PM fr.lip6.move.serialization.SerializationUtil serializePropertiesForITSCTLTools
INFO: Time to serialize properties into /home/mcc/execution/CTLFireability.ctl : 3 ms
Sequence of Actions to be Executed by the VM
This is useful if one wants to reexecute the tool in the VM from the submitted image disk.
set -x
# this is for BenchKit: configuration of major elements for the test
export BK_INPUT="TCPcondis-PT-05"
export BK_EXAMINATION="CTLFireability"
export BK_TOOL="itstoolsl"
export BK_RESULT_DIR="/tmp/BK_RESULTS/OUTPUTS"
export BK_TIME_CONFINEMENT="3600"
export BK_MEMORY_CONFINEMENT="16384"
# this is specific to your benchmark or test
export BIN_DIR="$HOME/BenchKit/bin"
# remove the execution directoty if it exists (to avoid increse of .vmdk images)
if [ -d execution ] ; then
rm -rf execution
fi
tar xzf /home/mcc/BenchKit/INPUTS/TCPcondis-PT-05.tgz
mv TCPcondis-PT-05 execution
cd execution
pwd
ls -lh
# this is for BenchKit: explicit launching of the test
echo "====================================================================="
echo " Generated by BenchKit 2-3637"
echo " Executing tool itstoolsl"
echo " Input is TCPcondis-PT-05, examination is CTLFireability"
echo " Time confinement is $BK_TIME_CONFINEMENT seconds"
echo " Memory confinement is 16384 MBytes"
echo " Number of cores is 4"
echo " Run identifier is r177-smll-152708747600179"
echo "====================================================================="
echo
echo "--------------------"
echo "content from stdout:"
echo
echo "=== Data for post analysis generated by BenchKit (invocation template)"
echo
if [ "CTLFireability" = "UpperBounds" ] ; then
echo "The expected result is a vector of positive values"
echo NUM_VECTOR
elif [ "CTLFireability" != "StateSpace" ] ; then
echo "The expected result is a vector of booleans"
echo BOOL_VECTOR
else
echo "no data necessary for post analysis"
fi
echo
if [ -f "CTLFireability.txt" ] ; then
echo "here is the order used to build the result vector(from text file)"
for x in $(grep Property CTLFireability.txt | cut -d ' ' -f 2 | sort -u) ; do
echo "FORMULA_NAME $x"
done
elif [ -f "CTLFireability.xml" ] ; then # for cunf (txt files deleted;-)
echo echo "here is the order used to build the result vector(from xml file)"
for x in $(grep '
echo "FORMULA_NAME $x"
done
fi
echo
echo "=== Now, execution of the tool begins"
echo
echo -n "BK_START "
date -u +%s%3N
echo
timeout -s 9 $BK_TIME_CONFINEMENT bash -c "/home/mcc/BenchKit/BenchKit_head.sh 2> STDERR ; echo ; echo -n \"BK_STOP \" ; date -u +%s%3N"
if [ $? -eq 137 ] ; then
echo
echo "BK_TIME_CONFINEMENT_REACHED"
fi
echo
echo "--------------------"
echo "content from stderr:"
echo
cat STDERR ;