About the Execution of Irma.struct for QuasiCertifProtocol-COL-02
| Execution Summary | |||||
| Max Memory Used (MB) |
Time wait (ms) | CPU Usage (ms) | I/O Wait (ms) | Computed Result | Execution Status |
| 443.390 | 50427.00 | 16118.00 | 993.20 | TFTTTFFTFTFFTTTT | normal |
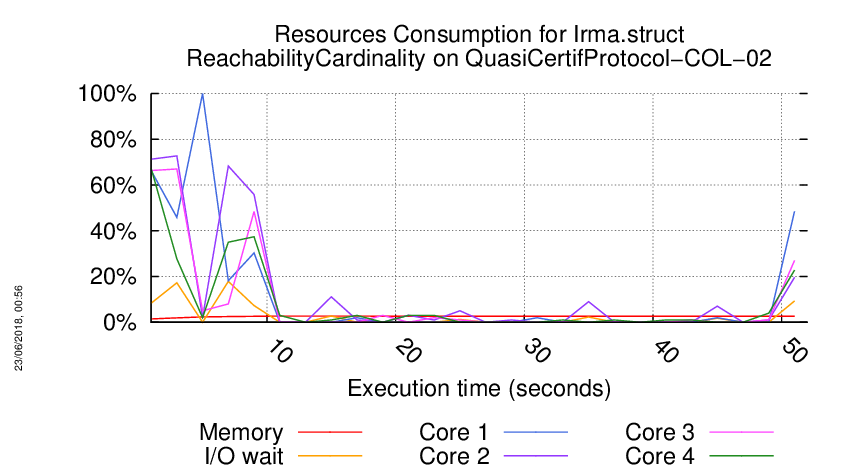
Execution Chart
We display below the execution chart for this examination (boot time has been removed).
Trace from the execution
Waiting for the VM to be ready (probing ssh)
.....................................................
/home/mcc/execution
total 204K
-rw-r--r-- 1 mcc users 3.9K May 15 18:54 CTLCardinality.txt
-rw-r--r-- 1 mcc users 22K May 15 18:54 CTLCardinality.xml
-rw-r--r-- 1 mcc users 3.3K May 15 18:54 CTLFireability.txt
-rw-r--r-- 1 mcc users 23K May 15 18:54 CTLFireability.xml
-rw-r--r-- 1 mcc users 4.0K May 15 18:50 GenericPropertiesDefinition.xml
-rw-r--r-- 1 mcc users 6.4K May 15 18:50 GenericPropertiesVerdict.xml
-rw-r--r-- 1 mcc users 2.5K May 26 09:27 LTLCardinality.txt
-rw-r--r-- 1 mcc users 11K May 26 09:27 LTLCardinality.xml
-rw-r--r-- 1 mcc users 2.1K May 26 09:27 LTLFireability.txt
-rw-r--r-- 1 mcc users 9.7K May 26 09:27 LTLFireability.xml
-rw-r--r-- 1 mcc users 3.4K May 15 18:54 ReachabilityCardinality.txt
-rw-r--r-- 1 mcc users 16K May 15 18:54 ReachabilityCardinality.xml
-rw-r--r-- 1 mcc users 117 May 15 18:54 ReachabilityDeadlock.txt
-rw-r--r-- 1 mcc users 355 May 15 18:54 ReachabilityDeadlock.xml
-rw-r--r-- 1 mcc users 2.7K May 15 18:54 ReachabilityFireability.txt
-rw-r--r-- 1 mcc users 14K May 15 18:54 ReachabilityFireability.xml
-rw-r--r-- 1 mcc users 1.8K May 15 18:54 UpperBounds.txt
-rw-r--r-- 1 mcc users 3.8K May 15 18:54 UpperBounds.xml
-rw-r--r-- 1 mcc users 5 May 15 18:50 equiv_pt
-rw-r--r-- 1 mcc users 3 May 15 18:50 instance
-rw-r--r-- 1 mcc users 5 May 15 18:50 iscolored
-rw-r--r-- 1 mcc users 34K May 15 18:50 model.pnml
=====================================================================
Generated by BenchKit 2-3637
Executing tool irma4mcc-structural
Input is QuasiCertifProtocol-COL-02, examination is ReachabilityCardinality
Time confinement is 3600 seconds
Memory confinement is 16384 MBytes
Number of cores is 4
Run identifier is r139-qhx2-152673581100012
=====================================================================
--------------------
content from stdout:
=== Data for post analysis generated by BenchKit (invocation template)
The expected result is a vector of booleans
BOOL_VECTOR
here is the order used to build the result vector(from text file)
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-00
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-01
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-02
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-03
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-04
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-05
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-06
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-07
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-08
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-09
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-10
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-11
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-12
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-13
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-14
FORMULA_NAME QuasiCertifProtocol-COL-02-ReachabilityCardinality-15
=== Now, execution of the tool begins
BK_START 1527780729587
BK_STOP 1527780780014
--------------------
content from stderr:
Prefix is 75f5f979.
Reading known information in /usr/share/mcc4mcc/75f5f979-known.json.
Reading learned information in /usr/share/mcc4mcc/75f5f979-learned.json.
Reading value translations in /usr/share/mcc4mcc/75f5f979-values.json.
Using directory /home/mcc/execution for input, as it contains a model.pnml file.
Using QuasiCertifProtocol-COL-02 as instance name.
Using QuasiCertifProtocol as model name.
Using algorithm or tool bmdt.
Model characteristics are: {'Examination': 'ReachabilityCardinality', 'Place/Transition': True, 'Colored': True, 'Relative-Time': 1, 'Relative-Memory': 1, 'Ordinary': True, 'Simple Free Choice': False, 'Extended Free Choice': False, 'State Machine': False, 'Marked Graph': False, 'Connected': True, 'Strongly Connected': False, 'Source Place': True, 'Sink Place': True, 'Source Transition': False, 'Sink Transition': False, 'Loop Free': True, 'Conservative': False, 'Sub-Conservative': False, 'Nested Units': False, 'Safe': False, 'Deadlock': True, 'Reversible': False, 'Quasi Live': None, 'Live': False}.
Known tools are: [{'Time': 148, 'Memory': 107.18, 'Tool': 'lola'}, {'Time': 186, 'Memory': 107.29, 'Tool': 'lola'}, {'Time': 195, 'Memory': 100.88, 'Tool': 'gspn'}, {'Time': 2370, 'Memory': 164.9, 'Tool': 'gspn'}, {'Time': 4928, 'Memory': 2228.58, 'Tool': 'marcie'}, {'Time': 5082, 'Memory': 307.54, 'Tool': 'itstools'}, {'Time': 5303, 'Memory': 300.84, 'Tool': 'itstools'}, {'Time': 5323, 'Memory': 2228.88, 'Tool': 'marcie'}].
Learned tools are: [{'Tool': 'lola'}].
Learned tool lola is 1.0x far from the best tool lola.
ReachabilityCardinality lola QuasiCertifProtocol-COL-02...
Time: 3600 - MCC
----- Start make prepare stdout -----
----- Start make prepare stderr -----
===========================================================================================
QuasiCertifProtocol-COL-02: translating COL Petri net model.pnml into LoLA format
===========================================================================================
translating COL Petri net complete
checking for too many tokens
===========================================================================================
QuasiCertifProtocol-COL-02: translating COL formula ReachabilityCardinality into LoLA format
===========================================================================================
translating formula complete
----- Start make result stdout -----
----- Start make result stderr -----
ReachabilityCardinality @ QuasiCertifProtocol-COL-02 @ 3540 seconds
----- Start make result stderr -----
----- Start make result stdout -----
lola: LoLA will run for 3540 seconds at most (--timelimit)
lola: NET
lola: reading net from model.pnml.lola
lola: finished parsing
lola: closed net file model.pnml.lola
lola: 142/65536 symbol table entries, 0 collisions
lola: preprocessing...
lola: finding significant places
lola: 86 places, 56 transitions, 55 significant places
lola: computing forward-conflicting sets
lola: computing back-conflicting sets
lola: 71 transition conflict sets
lola: TASK
lola: reading formula from QuasiCertifProtocol-COL-02-ReachabilityCardinality.task
lola: E (F (((p34 <= p35 + p36 + p37) AND (2 <= p41 + p43 + p42) AND ((p50 + p51 + p52 <= p69 + p68 + p70) OR (2 <= p34)) AND ((p54 <= p81) OR (p54 <= p41 + p43 + p42) OR (p3 <= p34))))) : A (G ((2 <= p38 + p39 + p40))) : E (F (((((2 <= p81) OR (1 <= p85)) AND (3 <= p38 + p39 + p40)) OR (p30 + p32 + p31 <= 1)))) : E (F ((p44 + p45 + p46 + 1 <= p81))) : E (F (TRUE)) : A (G ((p82 + p83 + p84 <= 2))) : A (G ((((p14 + p15 + p16 <= 2) OR (p44 + p45 + p46 <= 1)) AND (2 <= p57 + p56 + p55)))) : E (F ((3 <= p5 + p6 + p7 + p8 + p11 + p13 + p12 + p10 + p9))) : E (F ((3 <= p34))) : A (G (((p30 + p32 + p31 <= 1) OR (p57 + p56 + p55 <= 0)))) : A (G (((3 <= p38 + p39 + p40) AND (3 <= p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67) AND (1 <= p82 + p83 + p84) AND (p85 <= p14 + p15 + p16) AND (1 <= p14 + p15 + p16)))) : A (G ((2 <= p69 + p68 + p70))) : A (G (((p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= p38 + p39 + p40) OR (2 <= p75 + p76 + p77) OR (p54 <= p41 + p43 + p42) OR (p44 + p45 + p46 <= p57 + p56 + p55)))) : E (F (((p69 + p68 + p70 <= 1) AND (p33 + 1 <= p38 + p39 + p40) AND ((2 <= p35 + p36 + p37) OR (p38 + p39 + p40 <= p5 + p6 + p7 + p8 + p11 + p13 + p12 + p10 + p9) OR (p85 + 1 <= p81))))) : E (F (((p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= 1) AND (p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= 2) AND (p14 + p15 + p16 <= 2) AND (p44 + p45 + p46 <= 1)))) : E (F ((p81 <= 1)))
lola: computing a collection of formulas
lola: RUNNING
lola: subprocess 0 will run for 221 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F (((p34 <= p35 + p36 + p37) AND (2 <= p41 + p43 + p42) AND ((p50 + p51 + p52 <= p69 + p68 + p70) OR (2 <= p34)) AND ((p54 <= p81) OR (p54 <= p41 + p43 + p42) OR (p3 <= p34)))))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 24 literals and 6 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 0 markings, 0 edges
lola: ========================================
lola: subprocess 1 will run for 236 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G ((2 <= p38 + p39 + p40)))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: no
lola: produced by: state space
lola: The predicate is not invariant.
lola: 0 markings, 0 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality.sara
lola: ========================================
lola: subprocess 2 will run for 252 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F (((((2 <= p81) OR (1 <= p85)) AND (3 <= p38 + p39 + p40)) OR (p30 + p32 + p31 <= 1))))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 5 literals and 3 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 0 markings, 0 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-2.sara
lola: ========================================
lola: subprocess 3 will run for 272 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F ((p44 + p45 + p46 + 1 <= p81)))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 2 markings, 1 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-3.sara
lola: ========================================
lola: subprocess 4 will run for 295 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F (TRUE))
lola: ========================================
lola: SUBTASK
lola: checking initial satisfaction
lola: processed formula: TRUE
lola: processed formula length: 4
lola: 3 rewrites
lola: formula mentions 0 of 86 places; total mentions: 0
lola: closed formula file QuasiCertifProtocol-COL-02-ReachabilityCardinality.task
lola: processed formula with 0 atomic propositions
lola: RUNNING
lola: SUBRESULT
lola: result: yes
lola: produced by: preprocessing
lola: The net satisfies the property already in its initial state.
lola: 0 markings, 0 edges
lola: ========================================
lola: subprocess 5 will run for 321 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G ((p82 + p83 + p84 <= 2)))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: no
lola: produced by: state space
lola: The predicate is not invariant.
lola: 10 markings, 9 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-5.sara
lola: ========================================
lola: subprocess 6 will run for 354 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G ((((p14 + p15 + p16 <= 2) OR (p44 + p45 + p46 <= 1)) AND (2 <= p57 + p56 + p55))))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 3 literals and 2 conjunctive subformulas
lola: SUBRESULT
lola: result: no
lola: produced by: state space
lola: The predicate is not invariant.
lola: 0 markings, 0 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-6.sara
lola: ========================================
lola: subprocess 7 will run for 393 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F ((3 <= p5 + p6 + p7 + p8 + p11 + p13 + p12 + p10 + p9)))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-7.sara
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 23 markings, 22 edges
lola: ========================================
lola: state equation: calling and running sara
lola: subprocess 8 will run for 442 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F ((3 <= p34)))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-8.sara
lola: SUBRESULT
lola: result: no
lola: produced by: state space
lola: The predicate is unreachable.
lola: 372 markings, 446 edges
lola: ========================================
lola: subprocess 9 will run for 505 seconds at most (--localtimelimit=-1)
sara: try reading problem file QuasiCertifProtocol-COL-02-ReachabilityCardinality-7.sara.
lola: ========================================
lola: ...considering subproblem: A (G (((p30 + p32 + p31 <= 1) OR (p57 + p56 + p55 <= 0))))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 2 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is invariant.
lola: 38 markings, 62 edges
lola: ========================================
lola: subprocess 10 will run for 589 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G (((3 <= p38 + p39 + p40) AND (3 <= p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67) AND (1 <= p82 + p83 + p84) AND (p85 <= p14 + p15 + p16) AND (1 <= p14 + p15 + p16))))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: SUBRESULT
lola: state equation: Generated DNF with 5 literals and 5 conjunctive subformulas
lola: sara: place or transition ordering is non-deterministic
result: no
lola: produced by: state space
lola: The predicate is not invariant.
lola: 0 markings, 0 edges
lola: ========================================
lola: subprocess 11 will run for 707 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G ((2 <= p69 + p68 + p70)))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: no
lola: produced by: state space
lola: The predicate is not invariant.
lola: 0 markings, 0 edges
lola: ========================================
lola: subprocess 12 will run for 884 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: A (G (((p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= p38 + p39 + p40) OR (2 <= p75 + p76 + p77) OR (p54 <= p41 + p43 + p42) OR (p44 + p45 + p46 <= p57 + p56 + p55))))
lola: ========================================
lola: SUBTASK
lola: checking invariance
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 4 literals and 1 conjunctive subformulas
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-12.sara
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is invariant.
lola: 243 markings, 394 edges
lola: ========================================
lola: subprocess 13 will run for 1179 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F (((p69 + p68 + p70 <= 1) AND (p33 + 1 <= p38 + p39 + p40) AND ((2 <= p35 + p36 + p37) OR (p38 + p39 + p40 <= p5 + p6 + p7 + p8 + p11 + p13 + p12 + p10 + p9) OR (p85 + 1 <= p81)))))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 9 literals and 3 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 12 markings, 11 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-13.sara
lola: ========================================
lola: subprocess 14 will run for 1769 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F (((p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= 1) AND (p65 + p62 + p59 + p60 + p61 + p63 + p64 + p66 + p67 <= 2) AND (p14 + p15 + p16 <= 2) AND (p44 + p45 + p46 <= 1))))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 4 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 0 markings, 0 edges
lola: state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-14.sara
lola: ========================================
lola: state equation: calling and running saralola:
subprocess 15 will run for 3539 seconds at most (--localtimelimit=-1)
lola: ========================================
lola: ...considering subproblem: E (F ((p81 <= 1)))
lola: ========================================
lola: SUBTASK
lola: checking reachability
lola: Planning: workflow for reachability check: stateequation||search (--findpath=off)
lola: STORE
lola: using a bit-perfect encoder (--encoder=bit)
lola: using 220 bytes per marking, with 0 unused bits
lola: using a prefix tree store (--store=prefix)
lola: SEARCH (state space)
lola: state space: using reachability graph (--search=depth)
lola: state space: using reachability preserving stubborn set method with insertion algorithm (--stubborn=tarjan)
lola: RUNNING
lola: state equation: Generated DNF with 1 literals and 1 conjunctive subformulas
lola: SUBRESULT
lola: result: yes
lola: produced by: state space
lola: The predicate is reachable.
lola: 0 markings, 0 edges
lola: lola: RESULT
lola:
SUMMARY: yes no yes yes yes no no yes no yes no no yes yes yes yes
state equation: write sara problem file to QuasiCertifProtocol-COL-02-ReachabilityCardinality-15.sara
lola: ========================================
sara: try reading problem file QuasiCertifProtocol-COL-02-ReachabilityCardinality-14.sara.
sara: place or transition ordering is non-deterministic
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-0 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-1 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-2 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-3 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-4 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-5 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-6 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-7 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-8 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-9 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-10 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-11 FALSE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-12 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-13 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-14 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
FORMULA QuasiCertifProtocol-COL-02-ReachabilityCardinality-15 TRUE TECHNIQUES COLLATERAL_PROCESSING EXPLICIT STATE_COMPRESSION STUBBORN_SETS TOPOLOGICAL USE_NUPN
----- Kill lola and sara stdout -----
----- Kill lola and sara stderr -----
----- Finished stderr -----
----- Finished stdout -----
Sequence of Actions to be Executed by the VM
This is useful if one wants to reexecute the tool in the VM from the submitted image disk.
set -x
# this is for BenchKit: configuration of major elements for the test
export BK_INPUT="QuasiCertifProtocol-COL-02"
export BK_EXAMINATION="ReachabilityCardinality"
export BK_TOOL="irma4mcc-structural"
export BK_RESULT_DIR="/tmp/BK_RESULTS/OUTPUTS"
export BK_TIME_CONFINEMENT="3600"
export BK_MEMORY_CONFINEMENT="16384"
# this is specific to your benchmark or test
export BIN_DIR="$HOME/BenchKit/bin"
# remove the execution directoty if it exists (to avoid increse of .vmdk images)
if [ -d execution ] ; then
rm -rf execution
fi
tar xzf /home/mcc/BenchKit/INPUTS/QuasiCertifProtocol-COL-02.tgz
mv QuasiCertifProtocol-COL-02 execution
cd execution
pwd
ls -lh
# this is for BenchKit: explicit launching of the test
echo "====================================================================="
echo " Generated by BenchKit 2-3637"
echo " Executing tool irma4mcc-structural"
echo " Input is QuasiCertifProtocol-COL-02, examination is ReachabilityCardinality"
echo " Time confinement is $BK_TIME_CONFINEMENT seconds"
echo " Memory confinement is 16384 MBytes"
echo " Number of cores is 4"
echo " Run identifier is r139-qhx2-152673581100012"
echo "====================================================================="
echo
echo "--------------------"
echo "content from stdout:"
echo
echo "=== Data for post analysis generated by BenchKit (invocation template)"
echo
if [ "ReachabilityCardinality" = "UpperBounds" ] ; then
echo "The expected result is a vector of positive values"
echo NUM_VECTOR
elif [ "ReachabilityCardinality" != "StateSpace" ] ; then
echo "The expected result is a vector of booleans"
echo BOOL_VECTOR
else
echo "no data necessary for post analysis"
fi
echo
if [ -f "ReachabilityCardinality.txt" ] ; then
echo "here is the order used to build the result vector(from text file)"
for x in $(grep Property ReachabilityCardinality.txt | cut -d ' ' -f 2 | sort -u) ; do
echo "FORMULA_NAME $x"
done
elif [ -f "ReachabilityCardinality.xml" ] ; then # for cunf (txt files deleted;-)
echo echo "here is the order used to build the result vector(from xml file)"
for x in $(grep '
echo "FORMULA_NAME $x"
done
fi
echo
echo "=== Now, execution of the tool begins"
echo
echo -n "BK_START "
date -u +%s%3N
echo
timeout -s 9 $BK_TIME_CONFINEMENT bash -c "/home/mcc/BenchKit/BenchKit_head.sh 2> STDERR ; echo ; echo -n \"BK_STOP \" ; date -u +%s%3N"
if [ $? -eq 137 ] ; then
echo
echo "BK_TIME_CONFINEMENT_REACHED"
fi
echo
echo "--------------------"
echo "content from stderr:"
echo
cat STDERR ;