About the Execution of ITS-Tools for S_QuasiCertifProtocol-COL-02
| Execution Summary | |||||
| Max Memory Used (MB) |
Time wait (ms) | CPU Usage (ms) | I/O Wait (ms) | Computed Result | Execution Status |
| 354.920 | 11608.00 | 24592.00 | 272.90 | FFFFFFFFFFTFFFFF | normal |
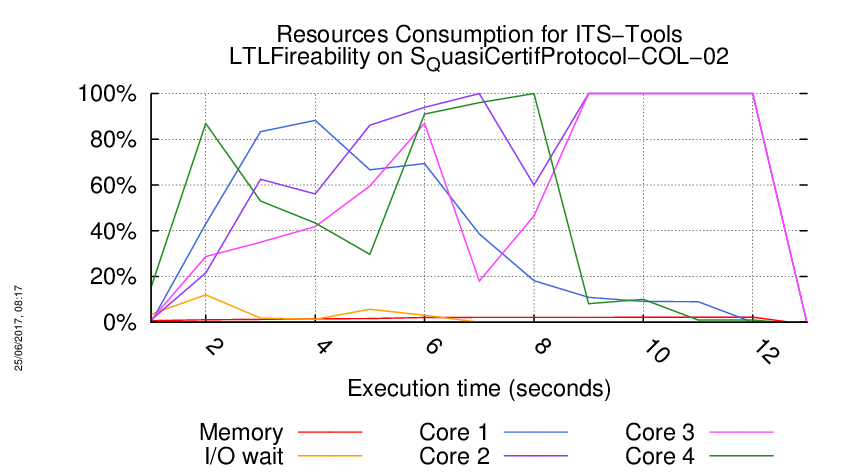
Execution Chart
We display below the execution chart for this examination (boot time has been removed).
Trace from the execution
Waiting for the VM to be ready (probing ssh)
............
=====================================================================
Generated by BenchKit 2-3254
Executing tool itstools
Input is S_QuasiCertifProtocol-COL-02, examination is LTLFireability
Time confinement is 3600 seconds
Memory confinement is 16384 MBytes
Number of cores is 4
Run identifier is r140-smll-149479233800195
=====================================================================
--------------------
content from stdout:
=== Data for post analysis generated by BenchKit (invocation template)
The expected result is a vector of booleans
BOOL_VECTOR
here is the order used to build the result vector(from text file)
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-0
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-1
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-10
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-11
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-12
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-13
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-14
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-15
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-2
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-3
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-4
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-5
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-6
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-7
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-8
FORMULA_NAME QuasiCertifProtocol-COL-02-LTLFireability-9
=== Now, execution of the tool begins
BK_START 1496392860610
Using solver YICES2 to compute partial order matrices.
Built C files in :
/home/mcc/execution
its-ltl command run as :
/home/mcc/BenchKit/eclipse/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.201705302212/bin/its-ltl-linux64 --gc-threshold 2000000 -i /home/mcc/execution/LTLFireability.pnml.gal -t CGAL -LTL /home/mcc/execution/LTLFireability.ltl -c -stutter-deadlock
Read 16 LTL properties
Checking formula 0 : !((X(G(((("tsid0.s3_0>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))||(("tsid1.s3_1>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1")))||(("tsid2.s3_2>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))))))
Formula 0 simplified : !XG(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s3_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s3_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s3_2>=1"))
Presburger conditions satisfied. Using coverability to approximate state space in K-Induction.
// Phase 1: matrix 56 rows 86 cols
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid1:n8_1 + -1'tsid0:Cstart_0 + 1'tsid1:Cstart_1= 0
invariant : -1'tsidxtsid0:n8_0 + -1'tsidxtsid0:n7_0 + 1'tsidxtsid2:n8_2 + 1'tsidxtsid2:n7_2= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid2:n9_2 + -1'tsidxtsid6:n9_6 + 1'tsidxtsid8:n9_8= 0
invariant : -1'tsidxtsid0:n8_0 + -1'tsidxtsid0:n7_0 + 1'tsidxtsid1:n8_1 + 1'tsidxtsid1:n7_1= 0
invariant : 1'tsidxtsid0:n8_0 + -1'tsidxtsid2:n8_2 + -1'tsidxtsid3:n8_3 + 1'tsidxtsid5:n8_5= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid2:n9_2 + -1'tsidxtsid3:n9_3 + 1'tsidxtsid5:n9_5= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid3:n9_3 + -1'tsid0:SstopOK_0 + 1'tsid1:SstopOK_1= 0
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid1:n8_1 + -1'tsidxtsid3:n7_3 + 1'tsidxtsid4:n7_4= 0
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid2:n8_2 + -1'tsidxtsid6:n7_6 + 1'tsidxtsid8:n7_8= 0
invariant : -2'tsidxtsid0:n9_0 + 1'tsidxtsid3:n9_3 + 1'tsidxtsid6:n9_6 + -1'malicious_reservoir:malicious_reservoir[0] + -1'CstopAbort:CstopAbort[0] + 1'tsid0:Sstart_0 + 1'tsid0:s2_0 + 1'tsid0:s3_0 + 1'tsid0:s4_0 + 1'tsid0:s5_0 + 1'tsid0:s6_0 + 3'tsid0:SstopOK_0 + 1'tsid1:Sstart_1 + 1'tsid1:s2_1 + 1'tsid1:s3_1 + 1'tsid1:s4_1 + 1'tsid1:s5_1 + 1'tsid1:s6_1 + 1'tsid2:Sstart_2 + 1'tsid2:s2_2 + 1'tsid2:s3_2 + 1'tsid2:s4_2 + 1'tsid2:s5_2 + 1'tsid2:s6_2= 2
invariant : 1'tsidxtsid2:n9_2 + -1'tsid0:SstopOK_0 + 1'tsid2:CstopOK_2= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid6:n9_6 + -1'tsid0:SstopOK_0 + 1'tsid2:SstopOK_2= 0
invariant : 1'malicious_reservoir:malicious_reservoir[0] + 1'CstopAbort:CstopAbort[0] + 1'SstopAbort:SstopAbort[0]= 1
invariant : 1'tsidxtsid0:n8_0 + -1'tsidxtsid1:n8_1 + -1'tsidxtsid6:n8_6 + 1'tsidxtsid7:n8_7= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsid0:SstopOK_0 + 1'tsid0:CstopOK_0= 0
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid2:n8_2 + -1'tsid0:Cstart_0 + 1'tsid2:Cstart_2= 0
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid2:n8_2 + -1'tsidxtsid3:n7_3 + 1'tsidxtsid5:n7_5= 0
invariant : 1'tsidxtsid1:n9_1 + -1'tsid0:SstopOK_0 + 1'tsid1:CstopOK_1= 0
invariant : -1'tsidxtsid0:n9_0 + 2'tsidxtsid0:n8_0 + -1'tsidxtsid1:n9_1 + -1'tsidxtsid1:n8_1 + -1'tsidxtsid2:n9_2 + -1'tsidxtsid2:n8_2 + 1'CstopAbort:CstopAbort[0] + 1'tsid0:c1_0 + 3'tsid0:Cstart_0 + 3'tsid0:SstopOK_0 + 1'tsid1:c1_1 + 1'tsid2:c1_2= 3
invariant : -1'tsidxtsid0:n8_0 + 1'tsidxtsid1:n8_1 + -1'tsidxtsid6:n7_6 + 1'tsidxtsid7:n7_7= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid1:n9_1 + -1'tsidxtsid3:n9_3 + 1'tsidxtsid4:n9_4= 0
invariant : 1'tsidxtsid0:n8_0 + -1'tsidxtsid1:n8_1 + -1'tsidxtsid3:n8_3 + 1'tsidxtsid4:n8_4= 0
invariant : 1'tsidxtsid0:n9_0 + -1'tsidxtsid1:n9_1 + -1'tsidxtsid6:n9_6 + 1'tsidxtsid7:n9_7= 0
invariant : 1'tsidxtsid0:n8_0 + -1'tsidxtsid2:n8_2 + -1'tsidxtsid6:n8_6 + 1'tsidxtsid8:n8_8= 0
invariant : 1'AstopAbort:AstopAbort[0] + 1'a5:a5[0] + 1'a4:a4[0] + 1'a3:a3[0] + 1'a2:a2[0] + 1'a1:a1[0] + 1'Astart:Astart[0] + 1'AstopOK:AstopOK[0]= 1
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
37 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.415006,33220,1,0,19005,3476,1056,17553,446,19235,56302
an accepting run exists (use option '-e' to print it)
Formula 0 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-0 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 1 : !((X(F(X(((("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid0.s2_0>=1"))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid1.s2_1>=1")))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid2.s2_2>=1")))))))
Formula 1 simplified : !XFX(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s2_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s2_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s2_2>=1"))
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.419236,33772,1,0,19273,3486,1088,17864,447,19245,57299
an accepting run exists (use option '-e' to print it)
Formula 1 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-1 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 2 : !((G((X("a2.a2[0]>=1"))U(F(F(((("tsid0.s3_0>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))||(("tsid1.s3_1>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1")))||(("tsid2.s3_2>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))))))))
Formula 2 simplified : !G(X"a2.a2[0]>=1" U F(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s3_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s3_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s3_2>=1")))
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
3 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.457847,36112,1,0,21808,3486,1101,20067,447,19677,65132
an accepting run exists (use option '-e' to print it)
Formula 2 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-2 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 3 : !((((("a3.a3[0]>=1")&&("tsid1.n4_1>=1"))&&("tsid2.n4_2>=1"))&&("tsid0.n4_0>=1")))
Formula 3 simplified : !("a3.a3[0]>=1" & "tsid0.n4_0>=1" & "tsid1.n4_1>=1" & "tsid2.n4_2>=1")
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.461071,36444,1,0,21853,3486,1123,20138,448,19699,65334
an accepting run exists (use option '-e' to print it)
Formula 3 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-3 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 4 : !(((F(F(G("a5.a5[0]>=1"))))U(F(("Astart.Astart[0]>=1")U(((("tsid0.Sstart_0>=1")&&("tsid0.n1_0>=1"))||(("tsid1.Sstart_1>=1")&&("tsid1.n1_1>=1")))||(("tsid2.Sstart_2>=1")&&("tsid2.n1_2>=1")))))))
Formula 4 simplified : !(FG"a5.a5[0]>=1" U F("Astart.Astart[0]>=1" U (("tsid0.Sstart_0>=1" & "tsid0.n1_0>=1") | ("tsid1.Sstart_1>=1" & "tsid1.n1_1>=1") | ("tsid2.Sstart_2>=1" & "tsid2.n1_2>=1"))))
1 unique states visited
0 strongly connected components in search stack
0 transitions explored
1 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.468255,37644,1,0,21880,3486,1178,20194,453,19699,65505
no accepting run found
Formula 4 is TRUE no accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-4 TRUE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 5 : !((X(X("a4.a4[0]>=1"))))
Formula 5 simplified : !XX"a4.a4[0]>=1"
5 unique states visited
5 strongly connected components in search stack
5 transitions explored
5 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.473652,37660,1,0,22032,3486,1181,20403,453,19719,66186
an accepting run exists (use option '-e' to print it)
Formula 5 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-5 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 6 : !((F(("Astart.Astart[0]>=1")U(F(X(((("tsid0.s2_0>=1")&&("tsid0.n3_0>=1"))||(("tsid1.s2_1>=1")&&("tsid1.n3_1>=1")))||(("tsid2.s2_2>=1")&&("tsid2.n3_2>=1"))))))))
Formula 6 simplified : !F("Astart.Astart[0]>=1" U FX(("tsid0.n3_0>=1" & "tsid0.s2_0>=1") | ("tsid1.n3_1>=1" & "tsid1.s2_1>=1") | ("tsid2.n3_2>=1" & "tsid2.s2_2>=1")))
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
2 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,0.490404,37928,1,0,22897,3496,1228,21300,457,19804,69194
an accepting run exists (use option '-e' to print it)
Formula 6 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-6 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 7 : !((G(G(G((((((("tsid0.s5_0>=1")&&("tsidxtsid1.n8_1>=1"))&&("tsidxtsid0.n8_0>=1"))&&("tsidxtsid2.n8_2>=1"))||(((("tsid1.s5_1>=1")&&("tsidxtsid4.n8_4>=1"))&&("tsidxtsid3.n8_3>=1"))&&("tsidxtsid5.n8_5>=1")))||(((("tsid2.s5_2>=1")&&("tsidxtsid7.n8_7>=1"))&&("tsidxtsid6.n8_6>=1"))&&("tsidxtsid8.n8_8>=1")))U(((("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid0.s6_0>=1"))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid1.s6_1>=1")))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid2.s6_2>=1"))))))))
Formula 7 simplified : !G((("tsid0.s5_0>=1" & "tsidxtsid0.n8_0>=1" & "tsidxtsid1.n8_1>=1" & "tsidxtsid2.n8_2>=1") | ("tsid1.s5_1>=1" & "tsidxtsid3.n8_3>=1" & "tsidxtsid4.n8_4>=1" & "tsidxtsid5.n8_5>=1") | ("tsid2.s5_2>=1" & "tsidxtsid6.n8_6>=1" & "tsidxtsid7.n8_7>=1" & "tsidxtsid8.n8_8>=1")) U (("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s6_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s6_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s6_2>=1")))
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.38727,43680,1,0,22897,3496,1470,21300,460,19806,69745
an accepting run exists (use option '-e' to print it)
Formula 7 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-7 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 8 : !((X(("a1.a1[0]>=1")U(X(F(((("tsid2.n2_2>=1")&&("tsid1.n2_1>=1"))&&("tsid0.n2_0>=1"))&&("a1.a1[0]>=1")))))))
Formula 8 simplified : !X("a1.a1[0]>=1" U XF("a1.a1[0]>=1" & "tsid0.n2_0>=1" & "tsid1.n2_1>=1" & "tsid2.n2_2>=1"))
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.39377,43680,1,0,23236,3496,1519,21734,461,19807,71529
an accepting run exists (use option '-e' to print it)
Formula 8 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-8 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 9 : !((G(F(X((("tsid0.s4_0>=1")||("tsid1.s4_1>=1"))||("tsid2.s4_2>=1"))))))
Formula 9 simplified : !GFX("tsid0.s4_0>=1" | "tsid1.s4_1>=1" | "tsid2.s4_2>=1")
33 unique states visited
33 strongly connected components in search stack
34 transitions explored
33 items max in DFS search stack
4 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.43419,43680,1,0,23438,3496,1555,24237,462,19876,78982
an accepting run exists (use option '-e' to print it)
Formula 9 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-9 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 10 : !((X(((("tsid2.n2_2>=1")&&("tsid1.n2_1>=1"))&&("tsid0.n2_0>=1"))&&("a1.a1[0]>=1"))))
Formula 10 simplified : !X("a1.a1[0]>=1" & "tsid0.n2_0>=1" & "tsid1.n2_1>=1" & "tsid2.n2_2>=1")
4 unique states visited
4 strongly connected components in search stack
4 transitions explored
4 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.43518,43680,1,0,23438,3496,1567,24237,462,19877,79012
an accepting run exists (use option '-e' to print it)
Formula 10 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-10 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 11 : !((G(((("tsid0.n6_0>=1")&&("tsid1.n6_1>=1"))&&("tsid2.n6_2>=1"))&&("a5.a5[0]>=1"))))
Formula 11 simplified : !G("a5.a5[0]>=1" & "tsid0.n6_0>=1" & "tsid1.n6_1>=1" & "tsid2.n6_2>=1")
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.43779,43680,1,0,23438,3496,1621,24237,463,19878,79089
an accepting run exists (use option '-e' to print it)
Formula 11 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-11 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 12 : !((F(F((F(((("tsid2.n2_2>=1")&&("tsid1.n2_1>=1"))&&("tsid0.n2_0>=1"))&&("a1.a1[0]>=1")))U(X(((("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid0.s6_0>=1"))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid1.s6_1>=1")))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid2.s6_2>=1"))))))))
Formula 12 simplified : !F(F("a1.a1[0]>=1" & "tsid0.n2_0>=1" & "tsid1.n2_1>=1" & "tsid2.n2_2>=1") U X(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s6_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s6_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s6_2>=1")))
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
8 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.51316,43680,1,0,31652,3499,1635,30349,463,19892,98930
an accepting run exists (use option '-e' to print it)
Formula 12 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-12 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 13 : !((F((G(F("a2.a2[0]>=1")))U((((((("tsidxtsid0.n7_0>=1")&&("tsidxtsid6.n7_6>=1"))&&("tsidxtsid3.n7_3>=1"))&&("tsid0.Cstart_0>=1"))||(((("tsidxtsid1.n7_1>=1")&&("tsidxtsid7.n7_7>=1"))&&("tsidxtsid4.n7_4>=1"))&&("tsid1.Cstart_1>=1")))||(((("tsidxtsid2.n7_2>=1")&&("tsidxtsid8.n7_8>=1"))&&("tsidxtsid5.n7_5>=1"))&&("tsid2.Cstart_2>=1")))U(((("tsid0.s3_0>=1")&&("tsid0.n5_0>=1"))||(("tsid1.s3_1>=1")&&("tsid1.n5_1>=1")))||(("tsid2.s3_2>=1")&&("tsid2.n5_2>=1")))))))
Formula 13 simplified : !F(GF"a2.a2[0]>=1" U ((("tsid0.Cstart_0>=1" & "tsidxtsid0.n7_0>=1" & "tsidxtsid3.n7_3>=1" & "tsidxtsid6.n7_6>=1") | ("tsid1.Cstart_1>=1" & "tsidxtsid1.n7_1>=1" & "tsidxtsid4.n7_4>=1" & "tsidxtsid7.n7_7>=1") | ("tsid2.Cstart_2>=1" & "tsidxtsid2.n7_2>=1" & "tsidxtsid5.n7_5>=1" & "tsidxtsid8.n7_8>=1")) U (("tsid0.n5_0>=1" & "tsid0.s3_0>=1") | ("tsid1.n5_1>=1" & "tsid1.s3_1>=1") | ("tsid2.n5_2>=1" & "tsid2.s3_2>=1"))))
2 unique states visited
2 strongly connected components in search stack
2 transitions explored
2 items max in DFS search stack
1 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.52854,43680,1,0,32727,3499,1682,31533,467,19893,102945
an accepting run exists (use option '-e' to print it)
Formula 13 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-13 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 14 : !((G(X((((("tsid0.n6_0>=1")&&("tsid1.n6_1>=1"))&&("tsid2.n6_2>=1"))&&("a5.a5[0]>=1"))U(X(((("tsid0.s4_0>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))||(("tsid1.s4_1>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1")))||(("tsid2.s4_2>=1")&&("malicious_reservoir.malicious_reservoir[0]>=1"))))))))
Formula 14 simplified : !GX(("a5.a5[0]>=1" & "tsid0.n6_0>=1" & "tsid1.n6_1>=1" & "tsid2.n6_2>=1") U X(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s4_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s4_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s4_2>=1")))
5 unique states visited
5 strongly connected components in search stack
5 transitions explored
5 items max in DFS search stack
3 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.57014,43680,1,0,33546,3499,1693,32333,467,19914,106370
an accepting run exists (use option '-e' to print it)
Formula 14 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-14 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Checking formula 15 : !((((("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid0.s6_0>=1"))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid1.s6_1>=1")))||(("malicious_reservoir.malicious_reservoir[0]>=1")&&("tsid2.s6_2>=1"))))
Formula 15 simplified : !(("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid0.s6_0>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid1.s6_1>=1") | ("malicious_reservoir.malicious_reservoir[0]>=1" & "tsid2.s6_2>=1"))
3 unique states visited
3 strongly connected components in search stack
3 transitions explored
3 items max in DFS search stack
0 ticks for the emptiness check
Model ,|S| ,Time ,Mem(kb) ,fin. SDD ,fin. DDD ,peak SDD ,peak DDD ,SDD Hom ,SDD cache peak ,DDD Hom ,DDD cachepeak ,SHom cache
STATS,0,6.57089,43680,1,0,33546,3499,1693,32333,467,19914,106372
an accepting run exists (use option '-e' to print it)
Formula 15 is FALSE accepting run found.
FORMULA QuasiCertifProtocol-COL-02-LTLFireability-15 FALSE TECHNIQUES DECISION_DIAGRAMS TOPOLOGICAL USE_NUPN
Exit code :0
BK_STOP 1496392872218
--------------------
content from stderr:
+ export BINDIR=/home/mcc/BenchKit/
+ BINDIR=/home/mcc/BenchKit/
++ pwd
+ export MODEL=/home/mcc/execution
+ MODEL=/home/mcc/execution
+ [[ LTLFireability = StateSpace ]]
+ /home/mcc/BenchKit//runeclipse.sh /home/mcc/execution LTLFireability -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -smt
+ ulimit -s 65536
+ java -Dosgi.requiredJavaVersion=1.6 -Xss8m -Xms40m -Xmx8192m -Declipse.pde.launch=true -Dfile.encoding=UTF-8 -classpath /home/mcc/BenchKit//eclipse/plugins/org.eclipse.equinox.launcher_1.3.201.v20161025-1711.jar org.eclipse.equinox.launcher.Main -application fr.lip6.move.gal.application.pnmcc -data /home/mcc/BenchKit//workspace -os linux -ws gtk -arch x86_64 -nl en_US -consoleLog -pnfolder /home/mcc/execution -examination LTLFireability -yices2path /home/mcc/BenchKit//yices/bin/yices -its -ltsminpath /home/mcc/BenchKit//lts_install_dir/ -smt
Jun 02, 2017 8:41:02 AM fr.lip6.move.gal.application.MccTranslator transformPNML
INFO: Parsing pnml file : /home/mcc/execution/model.pnml
Jun 02, 2017 8:41:02 AM fr.lip6.move.gal.pnml.togal.PnmlToGalTransformer transform
INFO: Detected file is not PT type :http://www.pnml.org/version-2009/grammar/symmetricnet
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.PnmlToGalTransformer transform
INFO: Load time of PNML (colored model parsed with PNMLFW) : 1355 ms
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.HLGALTransformer handlePage
INFO: Transformed 30 places.
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.HLGALTransformer handlePage
INFO: Computed order using colors.
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.HLGALTransformer handlePage
INFO: sort/places :tsidxtsid->n9,n8,n7,
Dot->malicious_reservoir,CstopAbort,SstopAbort,AstopAbort,a5,a4,a3,a2,a1,Astart,AstopOK,
tsid->n6,n5,n4,n3,n2,n1,c1,Cstart,Sstart,s2,s3,s4,s5,s6,SstopOK,CstopOK,
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.HLGALTransformer handlePage
INFO: Transformed 26 transitions.
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.pnml.togal.PnmlToGalTransformer transform
INFO: Computed order based on color domains.
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.application.MccTranslator applyOrder
INFO: Applying decomposition
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.instantiate.CompositeBuilder decomposeWithOrder
INFO: Decomposing Gal with order
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.instantiate.GALRewriter flatten
INFO: Flatten gal took : 77 ms
Jun 02, 2017 8:41:04 AM fr.lip6.move.gal.instantiate.CompositeBuilder rewriteArraysToAllowPartition
INFO: Rewriting arrays n9, n8, n7, n6, n5, n4, n3, n2, n1, c1, Cstart, Sstart, s2, s3, s4, s5, s6, SstopOK, CstopOK to variables to allow decomposition.
Jun 02, 2017 8:41:05 AM fr.lip6.move.gal.instantiate.Instantiator fuseIsomorphicEffects
INFO: Removed a total of 20 redundant transitions.
Jun 02, 2017 8:41:05 AM fr.lip6.move.serialization.SerializationUtil systemToFile
INFO: Time to serialize gal into /home/mcc/execution/LTLFireability.pnml.gal : 19 ms
Jun 02, 2017 8:41:05 AM fr.lip6.move.serialization.SerializationUtil serializePropertiesForITSLTLTools
INFO: Time to serialize properties into /home/mcc/execution/LTLFireability.ltl : 3 ms
Jun 02, 2017 8:41:05 AM fr.lip6.move.gal.gal2smt.bmc.KInductionSolver computeAndDeclareInvariants
INFO: Computed 25 place invariants in 32 ms
Jun 02, 2017 8:41:05 AM fr.lip6.move.gal.gal2smt.bmc.KInductionSolver init
INFO: Proved 86 variables to be positive in 426 ms
Jun 02, 2017 8:41:05 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver computeAblingMatrix
INFO: Computing symmetric may disable matrix : 56 transitions.
Jun 02, 2017 8:41:05 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of Completed :0/56 took 11 ms. Total solver calls (SAT/UNSAT): 4(2/2)
Jun 02, 2017 8:41:06 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of Completed :50/56 took 1050 ms. Total solver calls (SAT/UNSAT): 504(418/86)
Jun 02, 2017 8:41:07 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of Complete disable matrix. took 1306 ms. Total solver calls (SAT/UNSAT): 619(528/91)
Jun 02, 2017 8:41:07 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver computeAblingMatrix
INFO: Computing symmetric may enable matrix : 56 transitions.
Jun 02, 2017 8:41:07 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of Complete enable matrix. took 796 ms. Total solver calls (SAT/UNSAT): 619(91/528)
Jun 02, 2017 8:41:07 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver computeCoEnablingMatrix
INFO: Computing symmetric co enabling matrix : 56 transitions.
Jun 02, 2017 8:41:08 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of enabling matrix(22/56) took 1003 ms. Total solver calls (SAT/UNSAT): 1035(938/97)
Jun 02, 2017 8:41:09 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver printStats
INFO: Computation of Finished enabling matrix. took 1554 ms. Total solver calls (SAT/UNSAT): 1596(1403/193)
Jun 02, 2017 8:41:09 AM fr.lip6.move.gal.gal2smt.bmc.NecessaryEnablingsolver computeDoNotAccord
INFO: Computing Do-Not-Accords matrix : 56 transitions.
Jun 02, 2017 8:41:11 AM fr.lip6.move.gal.itstools.Runner runTool
INFO: Standard error output from running tool CommandLine [args=[/home/mcc/BenchKit/eclipse/plugins/fr.lip6.move.gal.itstools.binaries_1.0.0.201705302212/bin/its-ltl-linux64, --gc-threshold, 2000000, -i, /home/mcc/execution/LTLFireability.pnml.gal, -t, CGAL, -LTL, /home/mcc/execution/LTLFireability.ltl, -c, -stutter-deadlock], workingDir=/home/mcc/execution]
built 25 ordering constraints for composite.
Reverse transition relation is NOT exact ! Due to transitions malC1, malS6, malS5, malS4, malS3, malS2, malS1, malA5, malA3, malA4, malA2, malA1, Intersection with reachable at each step enabled. (destroyed/reverse/intersect/total) :0/30/12/42
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Computing Next relation with stutter on 47 deadlock states
Sequence of Actions to be Executed by the VM
This is useful if one wants to reexecute the tool in the VM from the submitted image disk.
set -x
# this is for BenchKit: configuration of major elements for the test
export BK_INPUT="S_QuasiCertifProtocol-COL-02"
export BK_EXAMINATION="LTLFireability"
export BK_TOOL="itstools"
export BK_RESULT_DIR="/tmp/BK_RESULTS/OUTPUTS"
export BK_TIME_CONFINEMENT="3600"
export BK_MEMORY_CONFINEMENT="16384"
# this is specific to your benchmark or test
export BIN_DIR="$HOME/BenchKit/bin"
# remove the execution directoty if it exists (to avoid increse of .vmdk images)
if [ -d execution ] ; then
rm -rf execution
fi
tar xzf /home/mcc/BenchKit/INPUTS/S_QuasiCertifProtocol-COL-02.tgz
mv S_QuasiCertifProtocol-COL-02 execution
# this is for BenchKit: explicit launching of the test
cd execution
echo "====================================================================="
echo " Generated by BenchKit 2-3254"
echo " Executing tool itstools"
echo " Input is S_QuasiCertifProtocol-COL-02, examination is LTLFireability"
echo " Time confinement is $BK_TIME_CONFINEMENT seconds"
echo " Memory confinement is 16384 MBytes"
echo " Number of cores is 4"
echo " Run identifier is r140-smll-149479233800195"
echo "====================================================================="
echo
echo "--------------------"
echo "content from stdout:"
echo
echo "=== Data for post analysis generated by BenchKit (invocation template)"
echo
if [ "LTLFireability" = "UpperBounds" ] ; then
echo "The expected result is a vector of positive values"
echo NUM_VECTOR
elif [ "LTLFireability" != "StateSpace" ] ; then
echo "The expected result is a vector of booleans"
echo BOOL_VECTOR
else
echo "no data necessary for post analysis"
fi
echo
if [ -f "LTLFireability.txt" ] ; then
echo "here is the order used to build the result vector(from text file)"
for x in $(grep Property LTLFireability.txt | cut -d ' ' -f 2 | sort -u) ; do
echo "FORMULA_NAME $x"
done
elif [ -f "LTLFireability.xml" ] ; then # for cunf (txt files deleted;-)
echo echo "here is the order used to build the result vector(from xml file)"
for x in $(grep '
echo "FORMULA_NAME $x"
done
fi
echo
echo "=== Now, execution of the tool begins"
echo
echo -n "BK_START "
date -u +%s%3N
echo
timeout -s 9 $BK_TIME_CONFINEMENT bash -c "/home/mcc/BenchKit/BenchKit_head.sh 2> STDERR ; echo ; echo -n \"BK_STOP \" ; date -u +%s%3N"
if [ $? -eq 137 ] ; then
echo
echo "BK_TIME_CONFINEMENT_REACHED"
fi
echo
echo "--------------------"
echo "content from stderr:"
echo
cat STDERR ;